 There has been a significant increase in DNS domain names containing blacklivesmatter or George Floyd’s name and there’s a good chance some of those are owned by people with malicious intent.
There has been a significant increase in DNS domain names containing blacklivesmatter or George Floyd’s name and there’s a good chance some of those are owned by people with malicious intent.
Social engineers and phishing creators love to use newsworthy events to foist new scams. They know that people’s interest in the latest events, natural or otherwise, makes potential victims less likely to be as skeptical when an unexpected email ends up in their inbox, especially if that email is enraging. Natural calamities like earthquakes, tornados, floods, and hurricanes have always been phishing draws. Pandemics, celebrity deaths, political upheaval, cultural unrest, and riots, are guaranteed to trick a higher number of unsuspecting victims into clicking on a malicious link or downloading a file that requires their password.
COVID-19 led to an extraordinary amount of new phishing. One vendor reported a 667% increase in coronavirus phishing emails in one month. One phishing campaign posed as a COVID-19 contact tracing app. Microsoft reported a malicious spreadsheet that posed as a COVID-19 death tracker. COVID-19 scams got so bad I published a blog article on how to tell the difference between legitimate and rogue COVID-19 emails with over a dozen examples of COVID-19 phishes.
Phishers Jump on the Bandwagon
A big indicator of whether or not phishers are going to jump on the current news bandwagon is how many DNS domains, legitimate or not, get registered with names related to the current news. A large number of newly registered domains indicates increased societal interest and the scam can more likely register their maliciously-inclined domain without drawing too much early attention. For example, over 20,000 domains related to COVID-19 were registered in just three weeks and 17% of them were related to maliciousness.
Blacklivesmatter Domains Registered
The current blacklivesmatter moment is another moment in history that spammers and phishers are sure to take advantage of. It’s newsworthy and will last for weeks. Cyber threat intelligence provider, WhoisXMLAPI, has looked at billions of domain registrations. They have noticed an uptick in domain registrations related to blacklivesmatter and George Floyd. The figure below shows a sampling of names.
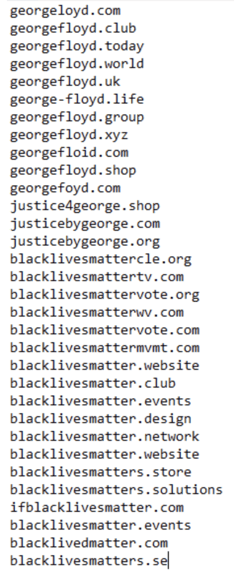
Out of all of the names that are registered, how many are for purely legit reasons and how many will be linked to some nefarious phishing campaign – we do not know. Although the georgeloyd.com domain is certainly depending on mis typing to score a visit. But if we look at the COVID-19 reports, the 17% scam rate is probably not to out of bounds. Once you start seeing the domain registrations come, the scammers are not far behind.
Disinformation Involved
Successful scammers like to use “stressor events” and to induce emotional responses. Stressor events are fake descriptions like, “If you don’t make the payment now, we will lose the business we’ve been working on for the last two years!” or “If you don’t confirm your email address and password, we will delete your account permanently!” They want the user to feel stress and to be more likely to skip past their normal procedures. They want to make the potential victim react right now. Fight or flight! The more time you give a victim, the more likely it is that they will check out the request another way to determine its legitimacy.
A very successful related tactic is that of emotional disinformation. For topics like BLM, where you have very strong emotions on both sides of the issue, scammers will pray on the intense feelings to motivate the person to respond, at all, and more quickly than if it was another topic that everyone agreed upon. In the COVID-19 phishing emails, scammers loved sending emails with topics like, “COVID-19 infection data was a hoax!” and “COVID-19 deaths significantly overstated” and “COVID-19 deaths significantly understated!” Disinformation campaigns don’t really care to be on one side or the other. They play both sides against each other. It’s not only scammers and phishers, but nation states and political groups. But scammers and phishers are certainly taking advantage of the disinformation campaigns that are sown into our digital world. News and social media sites are just now starting to deal with how to put down disinformation campaigns before they get widespread. And what they are finding out is that stopping malicious disinformation campaigns can be tough, especially in places where free speech and tolerance of extremist views are societally and legally protected.
Solution
So, what are you supposed to do? First, be aware and educate your employees that no ongoing news event will escape being used by scammers and phishers. It’s their life blood for getting people to click on emails and links that they otherwise would not. It has happened with every significant event before this year and has certainly happened with the COVID-19 pandemic. And it’s going to happen with the BLM movement and related controversies. Let your end users know to expect BLM-related phishing attacks, especially ones where their subjects try to elicit a quick, emotional response. In fact, we have a saying at KnowBe4: “If an email has a stressor event or emotional motivator in it, doubly Stop, and Think Before You Click on That Link!”




