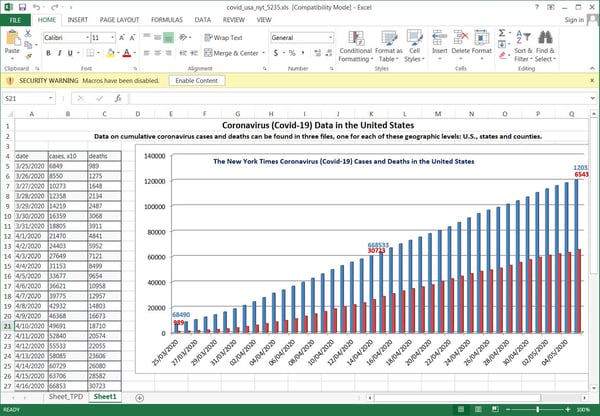
 Microsoft this week warned about a massive phishing attack that started on May 12. The campaign sends emails that look like they are from the "Johns Hopkins Center", and they have an Excel attachment that claims to be US deaths caused by the Coronavirus.
Microsoft this week warned about a massive phishing attack that started on May 12. The campaign sends emails that look like they are from the "Johns Hopkins Center", and they have an Excel attachment that claims to be US deaths caused by the Coronavirus.
If your user opens that infected "Excel doc", the file downloads a macro and runs the NetSupport Manager Remote Admin Tool. This is actually a legit remote support product, but it can also be used for criminal purposes, specifically to download malware on a targeted device. When installed, it allows the bad guys to gain complete control over the infected machine and execute commands on it remotely.
In a series of tweets, the Microsoft Security Intelligence team outlines how this massive campaign is spreading this tool. The Excel document contains malicious macros, and will prompt the user to 'Enable Content'. Once clicked, the macros will be executed to download and install the NetSupport Manager client from a remote site.
"The hundreds of unique Excel files in this campaign use highly obfuscated formulas, but all of them connect to the same URL to download the payload. NetSupport Manager is known for being abused by attackers to gain remote access to and run commands on compromised machines, Microsoft tweeted.
Short Technical Background
In this particular attack, the NetSupport Manager client is masquerading as the legitimate Desktop Windows Manager and executable will be saved as the dwm.exe file under a random %AppData% folder and launched. The bad guys will use the NetSupport Manager RAT to further compromise the user's machine by installing other malicious tools and scripts.
the NetSupport RAT used in this campaign further drops multiple components, including several .dll, .ini, and other .exe files, a VBScript, and an obfuscated PowerSploit-based PowerShell script. It connects to a C2 server, allowing attackers to send further commands," Microsoft explained.
What To Do About It
If you have any users that infected their machines you should operate under the assumption that their data has been compromised and that the threat actor attempted to steal their passwords. It is of course also possible that the threat actor used the infected machine to spread laterally throughout your network as a preparation for a full-network ransomware infection. Depending on the circumstances and your configuration, do a network-wide scan to prevent lateral penetration.
Whatever COVID ruse is being used, your users will wind up with either infected workstations at the house or in the office, giving out personal information or unleashing ransomware on your network. Give them a heads-up that especially now they need to stay on their toes with security top of mind.
I would send your employees, friends and family something like the following. Feel free to copy/paste/edit.
"This week, Microsoft warned about a massive phishing attack that looks like it is from Johns Hopkins University and has an Excel attachment which claims to have stats about the number of coronavirus deaths in America. If you open that attachment and click on 'Enable Content', it will download software that allows cybercriminals to take over your computer and steal confidential information. So don't open any Excel files from Johns Hopkins! NOTE: there will be more scams like this, so please remember to always Think Before You Click!
For KnowBe4 Customers, there are now 64 different Coronavirus-themed templates you can use to inoculate your users against this type of attack.
Let's stay safe out there, with millions of people working from home.
Warm regards,
Stu Sjouwerman
Founder and CEO, KnowBe4, Inc.





