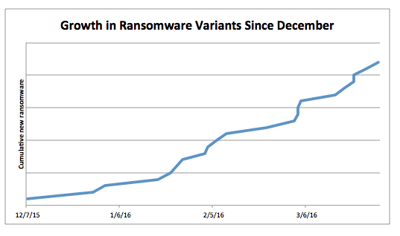
 If you've been in the IT trenches over the past year, you've probably noticed the announcements of new strains of ransomware are accelerating.
If you've been in the IT trenches over the past year, you've probably noticed the announcements of new strains of ransomware are accelerating.
The research team just published a blog post that confirms those impressions. It's not your imagination. Ransomware has indeed exploded, especially since the start of 2016. The FBI went public with yet another warning over the threat of ransomware.
2016 Ransomware: The New Roundup
So just how bad is it? New reports on the "rapid development of new strains of ransomware" is a good place to start. They document four new strains that their researchers have discovered in the wild just since early March:
- BrLock (mid April 2016)
- ROI Locker/Manamecrypt (early April 2016)
- CryptFlle2 (mid-March 2016)
- MM Locker (early March)
But these are just a subset of the new variants that have been discovered by the wider malware research community since the start of the year. The folks at Trend Micro also noticed this trend and created a graph to illustrate it:
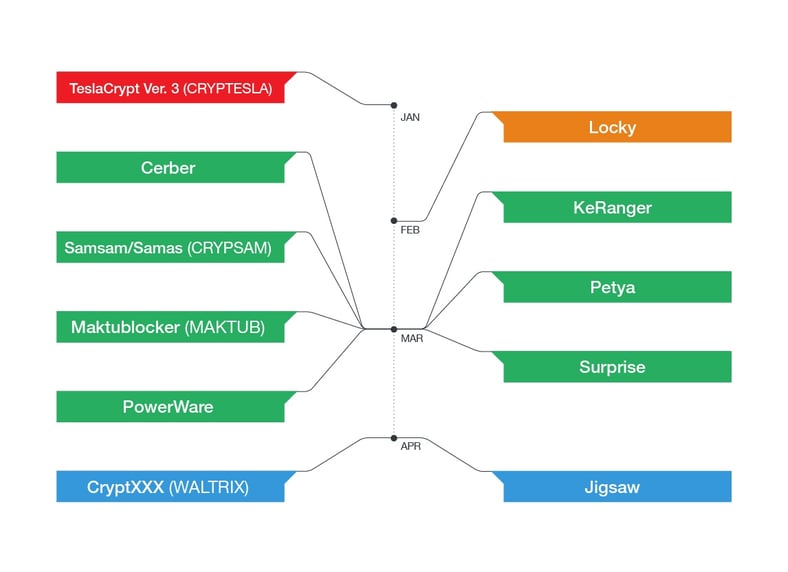
Eric Howes, KnowBe4's Principal Lab Researcher decided to take a trip down Q1 2016 memory lane by way of some of our favorite anti-malware blogs and websites. Here's a list of the various strains he found that were discovered by malware researchers just over the past four months!
TrueCrypter
Found in late April, this strain encrypts your data using AES-256 encryption and then demands about $115 in either bitcoins or an Amazon gift card. It could be a test ransomware though, as it appears that files are decrypted when you hit the 'Pay Now' button. Make sure you do a full backup before attempting decryption in case it fails.
CryptXXX
This ransomware is from the actors behind Reveton and was discovered in mid April. Through the Bedep Trojan, its 'information stealers' take a ton of data, it also steals Bitcoins!
7ev3n-HONE$T
A new version of the 7ev3n ransomware was first seen in mid April. It renames all of your files with the .R5A extension and demands 1 bitcoin or about $400 to decrypt, you can find more details about 7ev3n-HONE$T at Bleeping Computer. Unfortunately at this time there is no known free decryption process.
AutoLocky
Also discovered in mid-April, this strain tries to impersonate Locky ransomware by naming itself Locky and adding a .Locky extension to encrypted files. Although the method it's being distributed is unknown, there is a known decryption for AutoLocky.
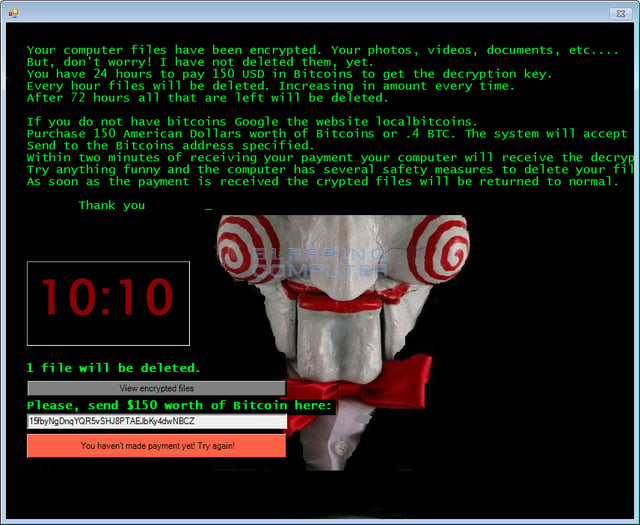
Released in early April, Jigsaw is the first ransomware that will delete files. A counter starts when you're infected, it starts with one per hour increasing every hour and will delete 1,000 files if and when the ransomware is restarted. The good news is there does seem to be a known decryption.
This ransomware was found in early April and instead of encrypting data like it claims, files are copied into a password-protected RAR file. However the password is pretty easy to determine so yes, there is a way to 'decrypt' CryptoHost.
Rokku
Rokku ransomware (found in late March) is being spread in email attachments and although there is no known free decryption, the ransom is relatively low at .24 bitcoins ($100 USD). Before payment is made you will be given a decryption key for one file to prove it can be done, however each file has its own key so to get all files back you will need to pay the ransom.
KimcilWare
This new strain of ransomware discovered in late March is targeted at websites on the Magneto eCommerce platform. Ransom is anywhere between $140 and $415, no known decryption for this one yet. A good reminder to make sure your website files are regularly backed up along with the rest of your files!
Coverton
This is an interesting ransomware strain first seen in late March. There is no known free decryption for Coverton, in addition to that it's been discovered that even if ransomware is being paid the files are not being properly decrypted! Proceed with caution and consult an expert when considering whether to pay the ransom.
Petya ransomware first surfaced in late March, infecting users through emails being directed at HR departments. This is different from most ransomware in that it locks up your entire hard drive rather than just encrypting files. Although there is a lot of information out there claiming there is a free decryption, you really can only remove the lock screen. Your files will remain infected until you pay the ransom - at this time it's .9 bitcoins.
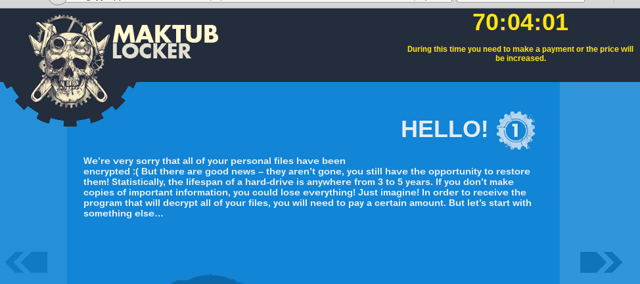
This new ransomware was discovered in mid March and is being spread via email through an attachment that appears to be an update Terms of Service document. Currently it's unknown whether there's a decryption method for Maktub. The ransom starts at 1.4 bitcoins then increases after a period of time, maxing out at 3.9 bitcoins.
Nemucod .CRYPTED
Nemucod is a malware family that in mid March has been found to download TeslaCrypt ransomware variants. Encryption of the files isn't highly sophisticated however, so there are steps you can take to restore your files from Nemucod ransomware.
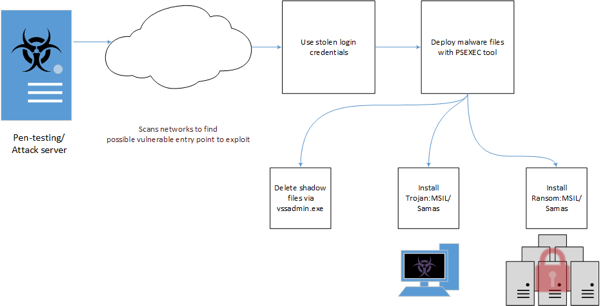
This new strain of Samas ransomware discovered in mid March attempts to infect entire networks. It starts with a pen-test/attack server that scans for vulnerabilities. It also incorporates Java-based vulnerabilities and other information stealing malware.
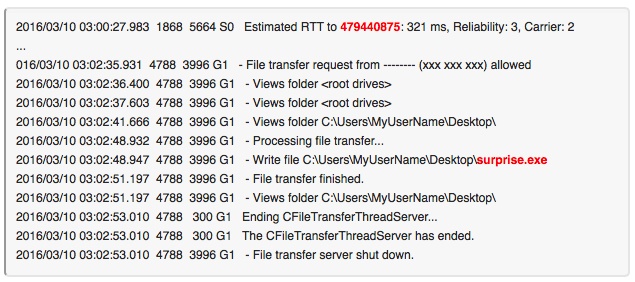
Surprise ransomware was first identified in mid March is installed via TeamViewer. It was initially thought that could have been caused by a data breach, however it appears that access was gained via victim credentials. What's interesting about Surprise ransom is the demand is between .5 to 25 bitcoins, depending on how important the files are.
Pompous
Seen in early March, Pompous ransomware's developer has a rather unique ransom note, bragging about how he'll never be caught and what the victim did wrong to get infected. Luckily there are decryption keys available for Pompous.
KeRanger
The first known Apple ransomware discovered in early March is spread through a hacked installer for Transmission. Apparently once installed, it will wait 3 days before file encryption occurs. The current recommendation from Transmission is to install version 2.91 which should detect and remove the infection.
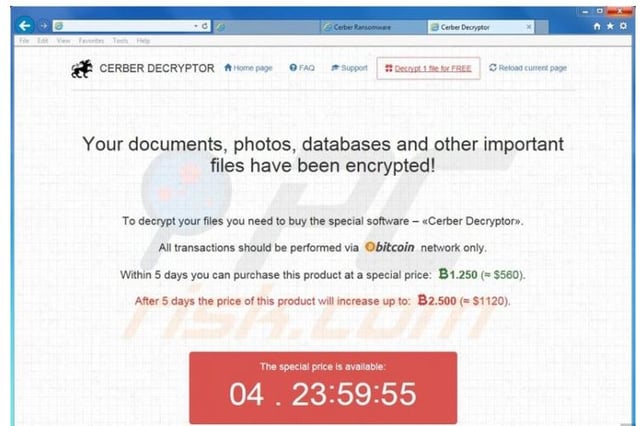
This new strain discovered in early March actually talks to its victims when one of the decrypt files are executed. Cerber is being sold as Ransomware-as-a-Service (RaaS), meaning practically anyone can pay to use it for an attack. Currently there is no known free decryption for Cerber ransomware.
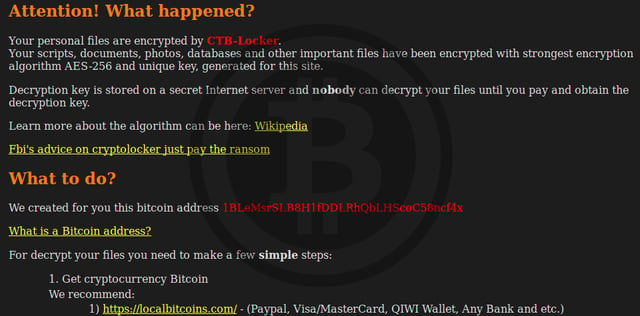
CTB-Locker for Websites
This variant of CTB-Locker or Critroni.A was first seen in mid February. Once website files are infected, a ransom of .4 bitcoins is demanded in exchange for the decryption key. Unfortunately, there is no free decryption method. If your website gets infected with CTB-Locker ransomware you should contact your hosting provider immediately to inquire about security and any backups you may have available.
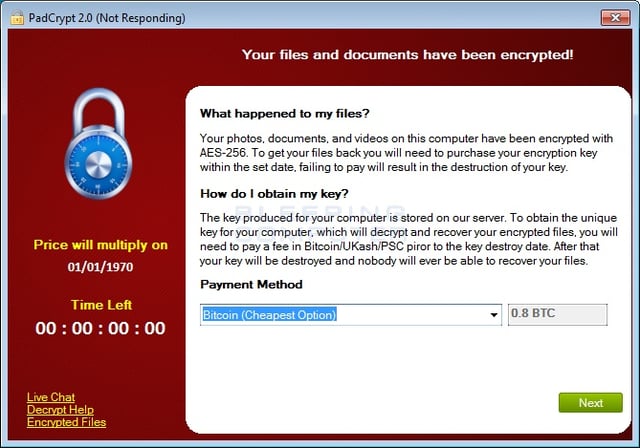
Padcrypt
First discovered in mid February, PadCrypt ransomware actually offers a live support chat feature and an uninstaller for victims. They are asking for a .8 bitcoin ransom (~$350), currently there is no way to decrypt the files for free.
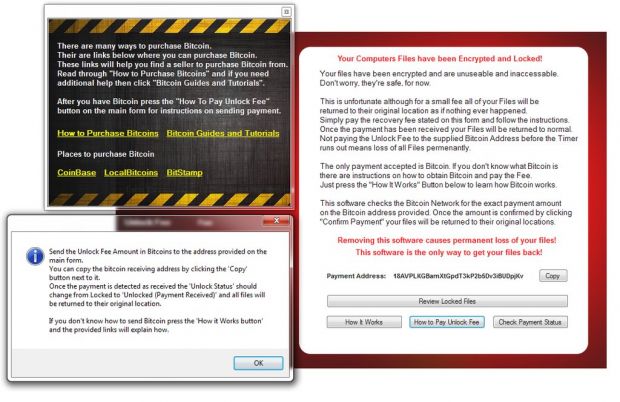
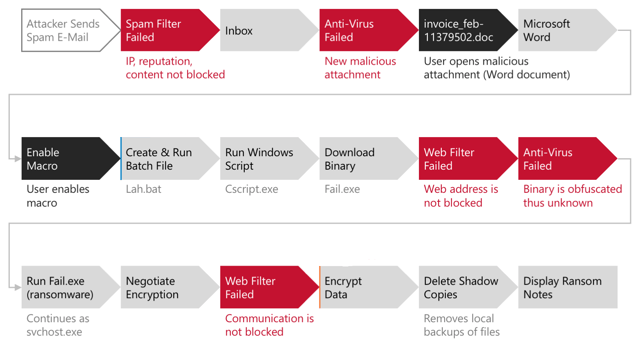
This strain first seen in mid February infects networks through malicious macros in Microsoft Word attachments. Victims are social engineered twice, first with an email with a message similar to ATTN: Invoice J-98223146. Once opened, there is a message stating to enable macros if the text can't be read. No known free decryption for Locky exists.
Umbrecrypt
This variant of CrypBoss discovered in early February uses AES encryption to infect selected files. No known free decryption for this one either, victims must email the hackers for payment instructions.
DMA Locker
The newest version found in early February goes after unmapped network shares and demands a payment of 4 bitcoins. There may be a way to decrypt DMA Locker ransomware by following a few simple steps.
NanoLocker
NanoLocker ransomware was first spotted in January and appears to attack through an email attachment that will throw up a fake PDF error message. There is a way to possibly decrypt files without paying the small ransom (~$43). The decryption key is temporarily stored until files are done being encrypted, so it definitely has to be done at the right time.
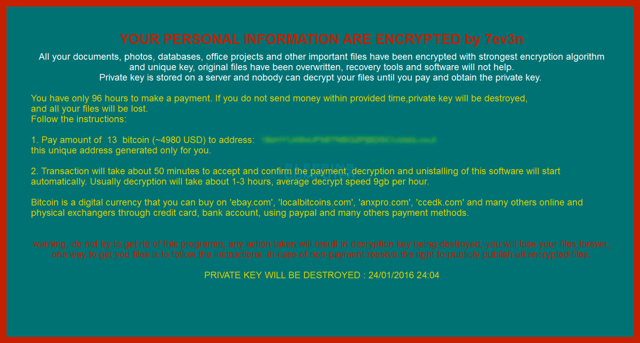
This ransomware strain discovered in late January encrypts files and also damages the Windows system it was installed on. What's worse is the actors are demanding 13 bitcoins or nearly $5,000 and there is no current free decryption.
LeChiffre
This strain was first seen in mid January and attacks by finding vulnerabilities remotely, then LeChiffre is run manually. The good news is there is a known decryption method for this ransomware.
Magic
New Magic ransomware discovered in mid January looks to be a copy of eda2 which the developer claims was made for educational purposes but is now being used maliciously. Ransom is 1 bitcoin.
CryptoJoker
First discovered in early January, this strain is likely distributed via phishing emails containing a disguised PDF. When encryption starts, CyrptoJoker scans for all drives including mapped network drives for certain file extensions. Victims must email the developers for payment instructions, no known free decryption method is yet known.
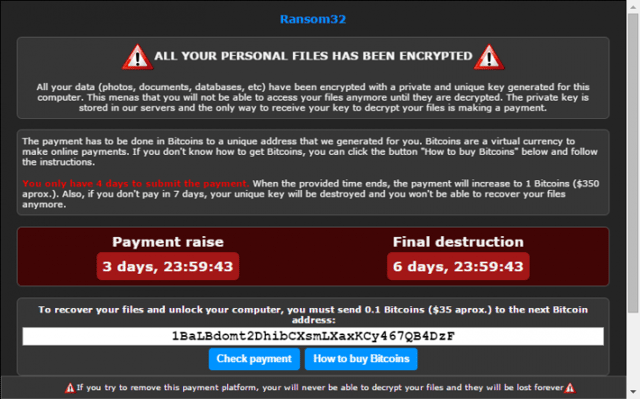
The first ransomware strain discovered this year in early January is also the first one written in Javascript. This is significant because it means one codebase can easily be implemented across Windows as well as Linux and Mac. Ransom32 RaaS has an affiliate program for cybercriminals with a full console where buyers can customize their own version of the ransomware.
We make no claims that the above list is complete, but it definitely demonstrates the alarming growth in new strains.
The sheer number of new ransomware variants that have emerged in the wild in 2016 increases the chances that both businesses and individuals will encounter this type of malware.
However, the sheer number of new strains is only part of the story. Many of these new variants are the products of new "copycat" actors trying to muscle into this new racket. These new actors bring with them new techniques and approaches, new attack vectors, new code platforms, and different ways to extort victims to cough up the ransom.
Lucky for us, "new and different", does not always mean more successful or dangerous. A lot of these new strains are flawed in design or execution. Malware researchers have exposed fatal flaws in a significant number of them, allowing them to discover or generate decryption keys that allow the liberation of users' files from their jailers.
In one case the author of a particular flavor was more interested in boasting about his skills than fireproofing his own code, allowing researchers to exploit a backdoor and recover the decryption keys. There is a surprising range of new entrants into this criminal business model:
Ransomware appears to have become the new 'Hello World' of malware with experienced actors and new players alike getting into the market. We are also observing new features, highlighted in some of the examples in this post, as well as a maturing black market for ransomware as illustrated by ... an underground forum advertisement for ROI Locker. This ad is fairly typical of this type of malware, as well as 'ransomware-as-a-service' offerings.
As we mentioned in a previous blog post, if you get hit with an infection, your first stop should be the new ID Ransomware site, which allows you to identify the particular strain you are dealing with and, when available, download decryption tools to recover your user's files and/or whole network shares if backups turn out to have failed.
Your Last Line Of Defense: Employees
Not every strain is poorly designed and coded, though. And you can't count on the availability of decryption tools, which usually only work for a limited time until the bad guys come out with a new version. Ransomware is now so successful and profitable that it has drawn in the largest, well-funded malware mafias who continue to furiously innovate in an attempt to grab market share from each other.
For every under skilled, overly confident new entrant into the ransomware market there is at least one extremely clever group of malicious actors capable of building effectively uncrackable crypto-prisons for your company's data. And when your data goes to malware jail, your organization suffers downtime, data loss, possible intellectual property theft, and in certain industries like healthcare, ransomware infections are now looked at to possibly be a HIPAA violation resulting in heavy fines.
With every new ransomware strain it becomes increasingly important to shore up your company's last line of defense: your employees. That means ensuring that your users have been given effective security awareness training to identify social engineering red flags, whether they come through malvertising on exploit-laced web pages or deviously crafted phishing emails that make it through your filters.
 This 26-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with ransomware. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:
This 26-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with ransomware. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:




