A new ransomware strain called CryptoHost was discovered, which claims that it encrypts your data and then demands a ransom of .33 bitcoins to get your files back (~140 USD at the current exchange rate) . These cybercrims took a shortcut though, your files are not encrypted but copied into a password protected RAR archive. They are also not very professional compared to other crypto-ransomware threat actors and the password created by this infection is relatively easily discovered so that you can get infected workstations recovered if there is no backup.
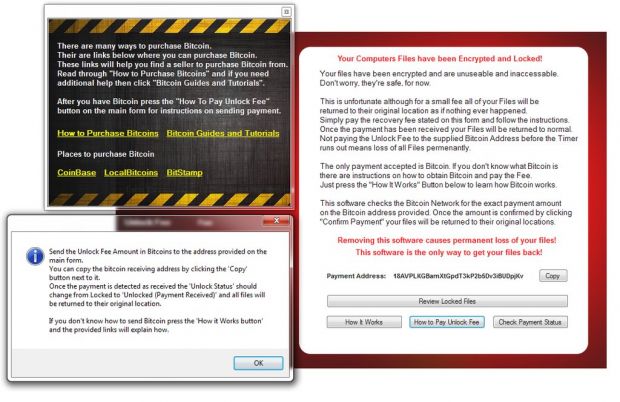
Also, CryptoHost doesn't use a Control & Command server, it only checks regularly if you've paid the ransom. The research team formed of MalwareForMe, MalwareHunterTeam, Michael Gillespie and Bleeping Computer have discovered a way to recover the RAR file's password and get your files back. To recover the files and unlock the archive, you need to stop the ransomware process with Windows Task Manager, find the cryptohost.exe process, stop it, and then unzip the RAR file. CryptoHost displays 3 images demanding ransom:
The bleepingcomputer blog has all the instructions on how to do this in greater detail. However, with any malware infection these days you do not know what other evil code is laid down on disk. Either run MalwareBytes to find it all and remove it, or wipe the machine and rebuild; it's better to be safe than sorry.
Get the most informative and complete hostage rescue manual on Ransomware. This 20-page manual (PDF) is packed with actionable info that you need to prevent infections, and what to do when you are hit with malware like this. You also get a Ransomware Attack Response Checklist and Prevention Checklist. (Updated March 2016)





