 Recently, Microsoft claimed that no known ransomware could penetrate the new Win10 Creators Update.
Recently, Microsoft claimed that no known ransomware could penetrate the new Win10 Creators Update.
Presenting new anti-ransomware protection features added in Win 10 CU, Robert Lefferts, Director of Program Management, Windows Enterprise and Security, said that no Windows 10 customer was affected by the recent WannaCry ransomware outbreak that took place in mid-May and no currently known ransomware strain can infect Windows 10.
ZDNet decided to not listen, but look for themselves. They hired a pro hacker and wanted to see if such a bold claim would hold up.
Spoiler alert: It didn't. "It's the macros, stupid!"
They hired Matthew Hickey, a security researcher and co-founder of cybersecurity firm Hacker House, and asked him a simple enough question: Will ransomware install on this operating system?
It took him a little over three hours to bust the operating system's various layers of security, but he got there.
Cracking Windows 10 S was a tougher task than expected, but one common attack point exists. Hickey was able to exploit how Microsoft Word, available to download from the Windows app store, handles and processes macros.
Hickey created a malicious, macro-based Word document on his own computer that when opened would allow him to carry out a reflective DLL injection attack, allowing him to bypass the app store restrictions by injecting code into an existing, authorized process.
In this case, Word was opened with administrative privileges through Windows' Task Manager, a straightforward process given the offline user account by default has administrative privileges.
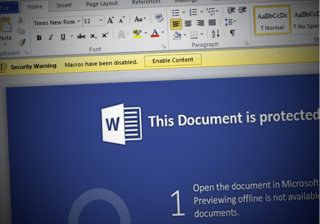
Hickey downloaded the malicious Word document he built from a network share, which Windows considers a trusted location, giving him permission to run the macro, so long as he enabled it from a warning bar at the top of the screen.
The document could easily point an arrow to the bar, telling the user to disable protected mode to see the contents of the document -- a common social engineering technique used in macro-based ransomware.
There you have it. Social engineering can get around the new Win10 protection. Better get those users trained, and keep them on their toes with security top of mind.
Here is the blow-by-blow at ZDNet.




