 There are a lot of scams in the world, and they seem to be proliferating at an exponential rate. My Facebook friend’s accounts are compromised all the time and I get sent scam requests for easy money. I get at least one scam message via SMS every day. My email inbox is full of phishing scams. I occasionally get phone calls from criminals claiming to be from my bank or some other local provider.
There are a lot of scams in the world, and they seem to be proliferating at an exponential rate. My Facebook friend’s accounts are compromised all the time and I get sent scam requests for easy money. I get at least one scam message via SMS every day. My email inbox is full of phishing scams. I occasionally get phone calls from criminals claiming to be from my bank or some other local provider.
I get emails from distraught people who have loved ones caught up in romance scams. Anyone trying to sell something on Craigslist quickly learns that it is overrun by scammers. If you apply for a job these days, there is a stronger chance that it is a scam job just trying to learn your personal details and get money from you. And who has not been approached by a cryptocurrency scammer claiming they can make you rich, rich, rich for just a small investment?
I think that maybe I am becoming more aware of all these scams as a side effect of being in the scam fighting security awareness training industry. But stats tell a different story.
- Phishing Attacks on Social Media Doubled Over 2021
- Average Ransoms Jump 130% While Use of Data Exfiltration Grows
- COVID-19 Test Related Phishing Scams Jump 521% Into January
- Malicious Office Documents Jump to 37% of All Malware Downloads at the End of 2021
- Ransomware Attacks are Growing in Number but not in Sophistication
There are more scams than ever coming at us more ways.
Protecting Your Organization Against Scams
I have people ask me what they can do to best protect themselves against social engineering and scams. At an organizational level, the answer is to implement the best defense-in-depth combination of policies, technical defenses and education to prevent social engineering; and education is usually the piece most lacking in the majority of organizations. I wrote about the 3 x 3 Pillars of Computer Security here.
If you want to know everything you can do to prevent social engineering and phishing, you can read my 49-page eBook or watch my one-hour webinar on the subject. Pick your poison. Both cover the same material, which is everything I and KnowBe4 could think of to fight social engineering and phishing – every policy, technical defense and security awareness training best practice we could think of, put into a small package.
Protecting Yourself, Co-Workers, Friends and Family
The best thing you can do, at the individual level, is to teach yourself (and everyone else) how to spot a scam. You want everyone to have a healthy level of skepticism and evaluate all incoming messages, no matter how they arrive (be it email, web, SMS, social media, voice calls, etc.), and look for potentially suspicious signs of a social engineering scam. A scam is a scam is a scam. Most scams have the following traits:
- They arrive unexpectedly
- The ask the receiver to do something the sender has never asked the receiver to do before
- They indicate a sense of urgency, claiming the receiver will be penalized if they do not take action immediately
- The requested action could be harmful to the receiver or their organization if the requested action is taken and is malicious
I have summarized the scam warning signs into the following flow chart below:
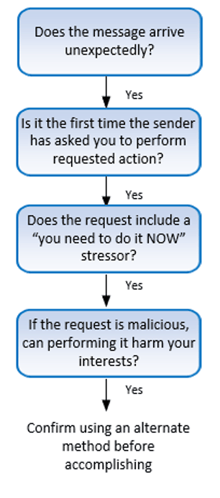
Teach yourself, your co-workers, your friends and family these four traits of scams. They should evaluate all incoming messages, no matter how they arrive, and see if the message has all of these traits. And if it does, then the receiver should confirm the validity of the request before performing any further actions. Please share this message and graphic with as many people as you can. We are all in this war against hackers and social engineers. Spread the message.
One note of caution. Not all scams contain all four traits. There are some advanced scams where these traits do not apply. For example, in a mortgage escrow scam, an intruder has usually successfully compromised a mortgage lender’s (or escrow agent’s) computer, scans for pending housing sales and then sends bogus bank money wiring instructions to the party buying the house on the day they were expecting to be told to make a loan escrow payment. The request arrives from the person they were expecting it to arrive from, on the day they were told to expect it, for the amount they were expected to have to pay to get the loan. Everything looks legit, but they do not know that the bank wiring account information leads to the attacker’s bank account.
So, not all scams have the four traits above, but 99% do. And teaching those four traits of scams will stop most of it. And we are working on the last 1%, but it is not as easy or consistent as most scams are to defeat. To defeat 99% of scams, it is mostly about education, and education about the four traits listed above.
Create a culture where everyone is always on the lookout for a possible scam. Let’s make it significantly harder for scammers to be successful. Now go fight the good fight!




