 Social engineering can come in many different forms: via email, websites, voice calls, SMS messages, social media and even fax. If it is a communication method, scammers and criminals are going to try to abuse it. Although the communication’s method may vary, the message the scammer is trying to convey has five traits in common.
Social engineering can come in many different forms: via email, websites, voice calls, SMS messages, social media and even fax. If it is a communication method, scammers and criminals are going to try to abuse it. Although the communication’s method may vary, the message the scammer is trying to convey has five traits in common.
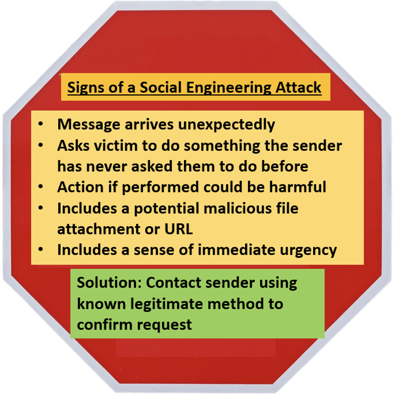
You can have legitimate emails that have all of these traits, but every message that has three or more of these traits is at higher risk for being involved in a social engineering attack than without the trait. Most social engineering attacks have all of these traits. Let’s discuss each high-risk trait in more detail.
1. Message Arrives Unexpectedly
There is almost never a time when the potential victim is expecting the message from the sender and certainly not about the involved subject. There are plenty of legitimate emails that arrive unexpectedly each day, but this is a key trait of most social engineering attacks. In fact, the opposite (i.e., you were expecting the message and its request), is a strong clue that it is not a social engineering scam.
But by itself, this trait alone does not always rule out a scam. For example, mortgage loan escrow scams, where the attacker has compromised a legitimate mortgage loan officer’s (or escrow officer’s) computer or email account and is asking for the borrower to send their escrow down payment to an illegitimate bank account is an example of that. The borrower was expecting the request from the officer for the requested amount and may not know or notice that the bank wiring instructions are bogus.
But in general, most social engineering schemes begin with the potential victim receiving an unexpected request.
2. Sender Asks Something Out of the Ordinary
In most cases, social engineering requests ask the potential victim to do something they have never done before. They want you to get money, send money, open a document, run an executable, send information, etc., that the (pretended) sender has never asked before.
Many phishing emails come from the legitimate email accounts of people we trust, but unbeknownst to potential victims, the sender’s email is under control of a malicious person. But even when that is the case, the fraudulent sender is asking the potential victim to perform an action that the legitimate sender has never asked the receiver to do before. Being asked to do something “net new” adds to the risk of performing the request.
3. Requested Action is Potentially Harmful
If the requested action is performed, could it be potentially harmful to the recipient or their organization? Being asked to open documents, execute programs, send information or put in passwords, are all examples of potentially harmful actions. If the request is something that would be difficult to create harm, even performed (e.g., pray for a person, write your government representative, etc.) then it is less likely to be social engineering.
4. Attacker Attaches an Unusual File or URL
Most digital social engineering attacks include a rogue link the user is told to click on or a document or program they are instructed to download (and open or execute). For example, a social engineering email request may simply request the potential victim send back personally identifiable information (e.g., “We need your banking information”, “Send us your SSN”, etc.). But most include potentially dangerous URL links, documents or content.
To learn how to spot potentially malicious rogue URL tricks, see my webinar or article.
The most common types of file formats used maliciously include: EXE, DLL, URL, SCR, HTA, HTM, HTML, MSI, SYS, ZIP, 7Z, BIN, CAB, CPL, and Microsoft Office document types (e.g., DOCX, XLSX, PPTX, etc.). You can find lots of “potentially dangerous file type lists on the Internet, including here. Attachments of fairly safe types of file formats (e.g., TXT, PDF, etc.) which do not include embedded URL links or “active content” are considered safer than others.
5. Attacker Includes a Sense of Urgency
Most scams include a heightened sense of urgency. We call these “stressor events”. The scammer wants to communicate a threat of harm (e.g., work, physical, financial, etc.) to the recipient if the potential victim does not move very quickly. Another reason why stressor events work is because the recipient is being motivated to move very quickly without time to consult other offsetting, authoritative resources.
If you receive a message with three or more of these high-risk traits, then stop, think and make sure it is not a social engineering scam before continuing.
Solution to Social Engineering Attacks
The easiest, quickest solution is to contact the sender on a known legitimate phone number to confirm the request or go directly to the purported vendor’s website using their legitimate URL and to see if the request is present on the vendor’s legitimate website as well. This one simple check would save billions of stolen dollars, save millions of unproductive hours, stress and heartache. Feel free to copy the graphic summary above (or this whole article) and send to end users.
Not all social engineering scams have all or most of these traits, but the vast majority do. Teaching everyone to be aware of these high-risk traits that might indicate social engineering is one of the most important things we can do to prevent cyber crime and social engineering attacks.




