 As the rate of ransomware attacks steadily increased over time, there are clear indicators as to how these attacks are starting and, therefore, what can be done to stop them.
As the rate of ransomware attacks steadily increased over time, there are clear indicators as to how these attacks are starting and, therefore, what can be done to stop them.
With the exception of the Verizon Data Breach Investigations Report, we rarely get insight into specific industry verticals. So, it’s refreshing to see a report focusing on a particular industry that can help provide some insight into the state of attack and security measures they can take to reduce the risk of becoming a victim.
In Sophos’ The State of Ransomware in Manufacturing and Production 2023 report, we find that over half (56%) of manufacturing organizations have experienced a ransomware attack – some successful, some stopped before damage could be done. The rate of such attacks has increased over time, with only 36% of manufacturing organizations experiencing attacks just two years ago. And, of those succumbing to an attack, 68% saw their data encrypted, and 73% used backups to restore the data.
The most interesting – and insightful – bit of detail from the report is the root causes of the attacks. According to the report, the number one root cause was compromised credentials – something usually accomplished by threat actors through social engineering attacks.
What’s more interesting is that if you take four of the 6 root causes shown below – phishing, malicious email, compromised credentials and download – you can conclude that email-based social engineering attacks remain a serious problem for manufacturing.
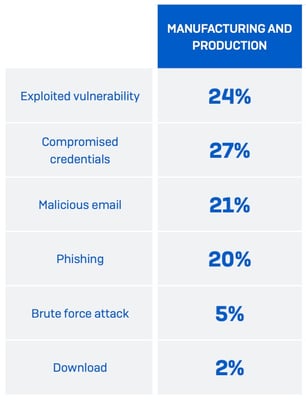
Source: Sophos
What’s needed is to educate users through Security Awareness Training about the various kinds of email-based attacks that can result in giving up credentials or unwittingly launching malware on their endpoint. If manufacturing can get a grasp on this problem, they’ll significantly reduce the number of attempted ransomware attacks.
 Here's how it works:
Here's how it works:




