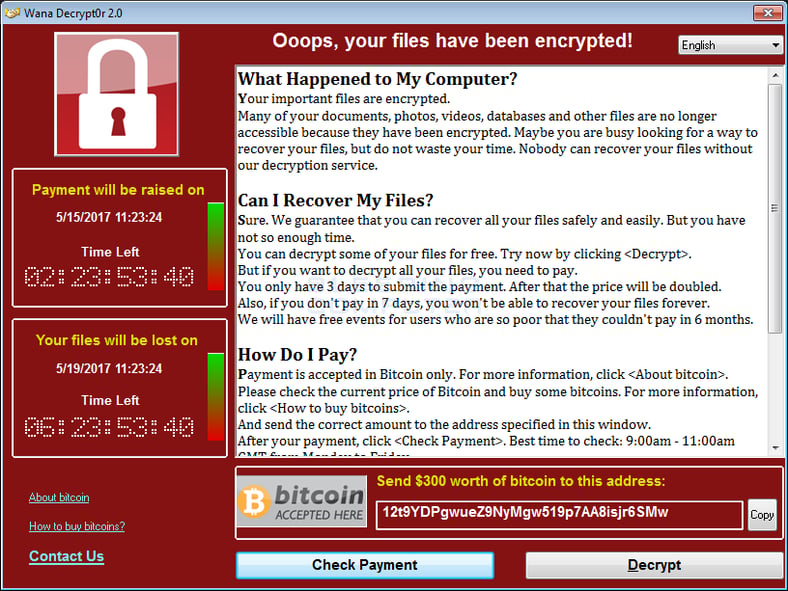
The strain is called "Wana Decrypt0r" which asks $300 from victims to decrypt their computers. This monster has infected hundreds of thousands of systems in more than 150 countries. Monday morning when people get back to work, these numbers will only go up. Check out an early animated map created by the NYTimes.
The Ransom Deadline Is Short
The ransom starts at $300 for the first 6 hours, and you've got up to 3 days to pay before it doubles to $600. If you don't pay within a week then the ransomware threatens to delete the files altogether. Note the social engineering aspect here too: a sense of urgency is created to prompt people into action. A sense of hope is granted by virtue of the ability to decrypt a sample selection of the files.
The ransomware's name is WCry, but is also referenced online under various names, such as WannaCry, WannaCrypt0r, WannaCrypt, or Wana Decrypt0r. As everybody keeps calling it "Wana Decrypt0r," this is the name we'll use in this article, but all are the same thing, which is version 2.0 of the lowly and unimpressive WCry ransomware that first appeared in March."
Kaspersky Lab also reports that the Wana strain has numerous languages available and was designed to affect multiple countries.
How To Detect The Presence Of Wana And SMBv1 Servers On Your Network
One of the easiest ways to monitor what is happening on your network is to setup a SPAN\Mirror port or use a network TAP. This will give you access to flows and packet payloads so you can see who is connecting to what and if there is anything suspicious moving around. Check out this blog post if you use Cisco switches, it explains how you can monitor multiple network segments without the need to remember what is connected to what switch port. If you don’t use Cisco switches there is an excellent resource on the Wireshark wiki site which looks at how to setup monitoring on other switches.
There is one caveat though, this infection moves out like lightning from patient zero, and all vulnerable machines are literally locked in less than two minutes so monitoring alone would not be enough to be stop this monster. Here is a video showing a machine on the left infected with MS17-010 worm, spreading WCry ransomware to machine on the right in real time.
There Are Four Things To Watch Out For When It Comes To Detecting Wana
- Check for SMBv1 use
- Check for an increase in the rate of file renames on your network
- Check for any instances of the file @Please_Read_Me@.txt on your file shares
- Check for any instances of files with these extensions
- .wnry
- .wcry
- .wncry
- .wncryt
If Your Network Has Been Infected, What To Do?
This ransomware strain cannot be decrypted with free tools. Research shows the encryption is done with RSA-2048 encryption. That means that decryption will be next to impossible, unless the coders have made a mistake that has not been found yet.
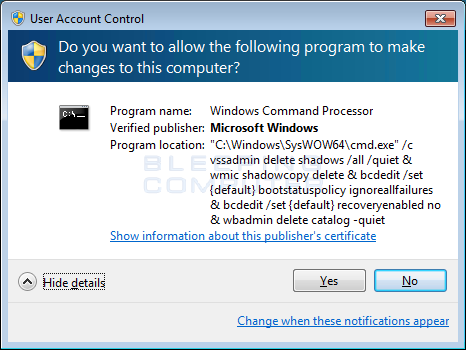
Your best bet is to recover from backups, and if your backup failed or does not exist, try a program like Shadow Explorer to see if the ransomware did not properly delete your Shadow Volume Copies. If a user did not click Yes at the UAC prompt, then there is a chance those are still available to start the recovery. Here is How to recover files and folders using Shadow Volume Copies. As a last resort and all backups have failed, you could decide to pay and get the files decrypted. It appears to work.
What Can Be Done To Stop Cybercriminals?
It's possible but difficult. Some bitcoin has reportedly been paid into hackers' accounts and investigators can track the money and see where the bitcoin ends up. “Despite what people tend to think, it's highly traceable,” Clifford Neuman, who directs the University of Southern California's Center for Computer Systems Security, told the Washington Post.
However, hackers are still able to hide and launder the bitcoins in many different ways. Investigators will also examine the code itself as hackers often leave identifiable traces of their work. You can watch as some of these wallets are receiving money in real time. There is an international manhunt underway.
Here Are 8 Things To Do About It (apart from having weapons-grade backups)
- Check your firewall configuration and make sure no criminal network traffic from port TCP/445 is allowed out, and disable SMBv1 on all machines immediately, and If possible, block 445 inbound to all internet-facing Windows systems
- From here on out with any ransomware infection, wipe the machine and re-image from bare metal
- If you have no Secure Email Gateway (SEG), get one that does URL filtering and make sure it's tuned correctly
- Make sure your endpoints are patched religiously, OS and 3rd Party Apps
- Make sure your endpoints and web-gateway have next-gen, frequently updated (a few hours or shorter) security layers
- Identify users that handle sensitive information and enforce some form of higher-trust authentication (like 2FA)
- Review your internal security Policies and Procedures, specifically related to financial transactions to prevent CEO Fraud
- Deploy new-school security awareness training, which includes simulated social engineering tests via multiple channels, not just email.
KnowBe4 enables your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
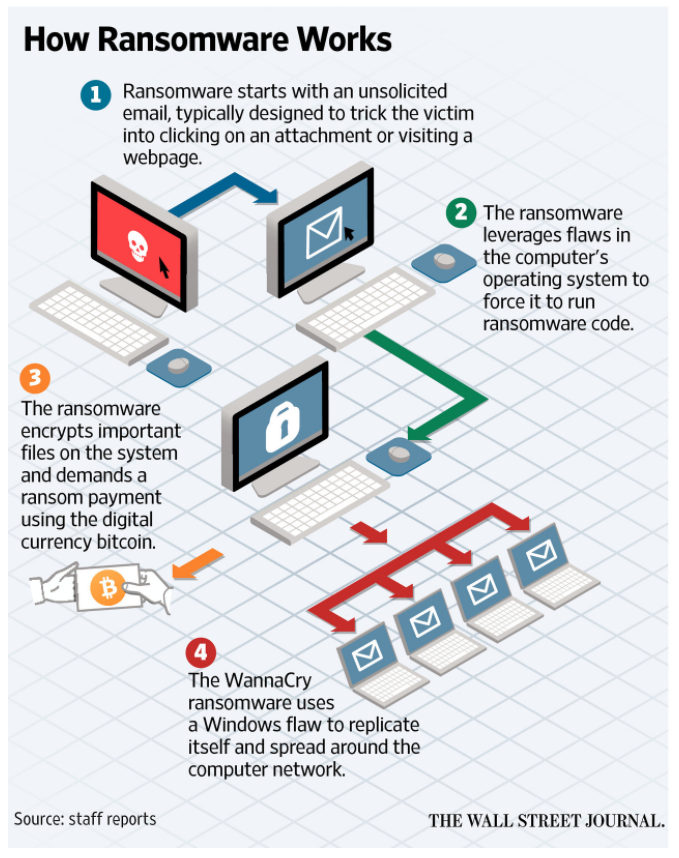
 Here's how it works:
Here's how it works:




