By Eric Howes, KnowBe4's Principal Lab Researcher
So you've subscribed to Security Awareness Training that includes training modules as well as simulated phishing campaigns for your organization. You may have gotten to the point where you're rolling out the training modules to your employees and setting up your very first phishing campaign to establish a baseline Phish Prone Percentage. But you're now wondering: what can your organization expect? Does this stuff really work? Are you going to see any kind of actual payoff from this training?
The answer is: yes, absolutely. There is a very real payoff, and your organization will benefit from the training modules and simulated phish campaigns almost immediately. One of our customers saw a just such a payoff from their training and phishing campaigns this past week when one of their employees got hit with a CEO Fraud phishing email.
CEO Fraud Phishing
CEO Fraud phishes usually take the form of fraudulent emails in which the bad guys spoof senior executives within a company in order to trick unwitting users, often from accounting or finance departments, into coughing up money or sensitive data. The most common form of CEO Fraud phishing that we see involves requests for wire transfers to bank accounts controlled by the bad guys. Another common phish we've seen over the past few months involves requests to send copies of employees' W-2 forms to the bad guys, who then exploit that data to file fraudulent tax returns and claim refunds.
CEO Fraud phishes are typically very well-targeted -- meaning, the bad guys have done research into the targeted company, determining which executives to spoof and which employees to target. These are not mass "spray-and-pray" spam campaigns. They are the product of strategy and preparation. And woe to the organization that dismisses the risk or fails to prepare their employees for this type of attack. As Brian Krebs recently noted, CEO Fraud emails have been on the rise, prompting the FBI to issue an alert.
A Classic Phish
This past week an employee at one of our customers was the target of a classic CEO Fraud phish. This employee, who we'll call Mandy, received the following phish email from an individual purporting to be the president of the company:
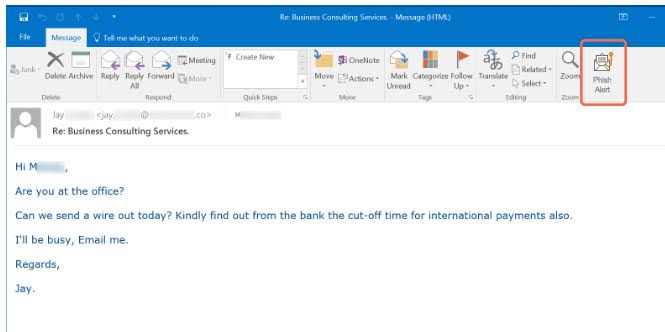
This phish is fairly representative of the CEO Fraud phishes that we see. It's short, direct, casual, and familiar, as most inter-office emails are. The request for a wire transfer is coupled with other details designed to make the entire email believable. More importantly, the bad guy discourages attempts by the employee to follow up on the request in person or via phone ("I'll be busy, Email me.")
What's also important to note is the domain name being used by the bad guys for this attack. Although we've obscured it, that domain is a look-alike for the targeted company's actual domain. The bad guys went so far as to register a version of the company's domain, only with the .CO (Columbia) Top Level Domain -- a common choice for bad guys trying to spoof .COM domains, as in this case. And that domain was in fact registered the very same day that Mandy received the initial phish email.
Mandy initially responded to the phishing email, indicating that the requested wire transfer was do-able:
Yes I am here. I'm sure we can. Do we have the information to pay from? I believe the cut-off is 2:30pm.
Shortly after responding to the bad guys, however, Mandy had doubts about the authenticity of the email. Just two weeks earlier Mandy had gone through her company's scheduled KnowBe4 Security Awareness Training. Using what she had learned, Mandy decided to return to that phish email and click KnowBe4's free Phish Alert Button (PAB), which her company had installed in users' instances of Outlook. By clicking the Phish Alert Button, Mandy alerted the company's IT staff to the phish she had received.
When Mandy failed to proceed with the wire transfer, she received yet another email from the bad guys, who were following up on what they must have thought was a nearly successful CEO Fraud operation:
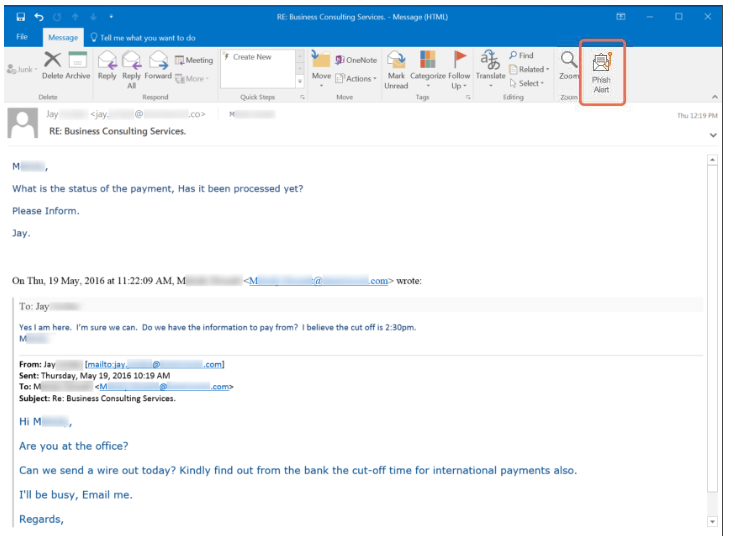
Notice that in this follow-up the bad guys carefully edited the domain that appears in the copy of the original email towards the bottom, changing the .CO TLD to a .COM to throw off anyone else who might look through this version of the email chain.
Again, Mandy clicked the Phish Alert Button (PAB) in Outlook, alerting IT staff to the follow-up email from the bad guys. The company's IT staff went directly to Mandy and confirmed what Mandy had suspected -- that this was indeed a phish attempt.
A Close Call
Although the bad guys never specified a requested amount of money to transfer in this case, the company stood to lose a significant chunk of change. Again, Brian Krebs:
The FBI estimates that organizations victimized by CEO fraud attacks lose on average between $25,000 and $75,000. But some CEO fraud incidents over the past year have cost victim companies millions — if not tens of millions — of dollars.
When we talked with this customer about Mandy's brush with CEO Fraud, the customer noted that it had recently put out a press release extolling the company's record quarterly performance, and that press release got picked up in stories on a number of online business news sites. We suspect the bad guys saw that press release and decided to help themselves to the company's recent influx of cash.
Every aspect of this incident is typical of the CEO Fraud phishes we see: the well-researched targeting of specific employees, the look-alike domain name, the personalized follow-up email, etc. What's also typical is the fact that the company's other security solutions failed to stop this phish from landing in Mandy's inbox. In our experience, anti-virus and anti-spam solutions are notoriously bad in flagging these kinds of attacks.
What stopped this attack was the "human firewall" the company had built using KnowBe4's training modules, simulated phishing platform, and Phish Alert Button. And the critical link in that "human firewall" had received their Security Awareness Training just two weeks earlier. Despite being only recently introduced to these kinds of attacks, this employee held the line, saving the company what would have almost certainly been a very large loss of money.
Get your own free Phish Alert Button (PAB) here. Available for Outlook and Outlook 365. PABs for Gmail and Notes are expected in a few weeks.
PS: Don't like to click on redirected buttons? Cut/Paste this link in your browser:
https://www.knowbe4.com/free-phish-alert





