Using a mix of fake admin alerts and a spoofed logon page, this newest campaign leverages IT’s urgency in fixing critical issues before they impact users.
Cybercriminals that use phishing as their attack of choice know two things make a successful campaign: context and urgency. In this latest attack covered over at Bleeping Computer, it looks like scammers have figured out the perfect angle to include both.
Using fake Office 365 alerts citing expiration of licenses or an issue that requires investigation, the bad guys are hoping to take advantage of IT’s desire to make certain Office 365 is available and licensed. With around half of all businesses using Office 365, this tactic makes a lot of sense – the phishing email is applicable to as much as half of all recipients (assuming they are all IT pros), and the alert aspect creates the urgency needed to trick IT into clicking the link.
IT pros are taken to an Azure-based windows.net site that mimics Office 365’s logon that even uses an SSL certificate published by Microsoft:
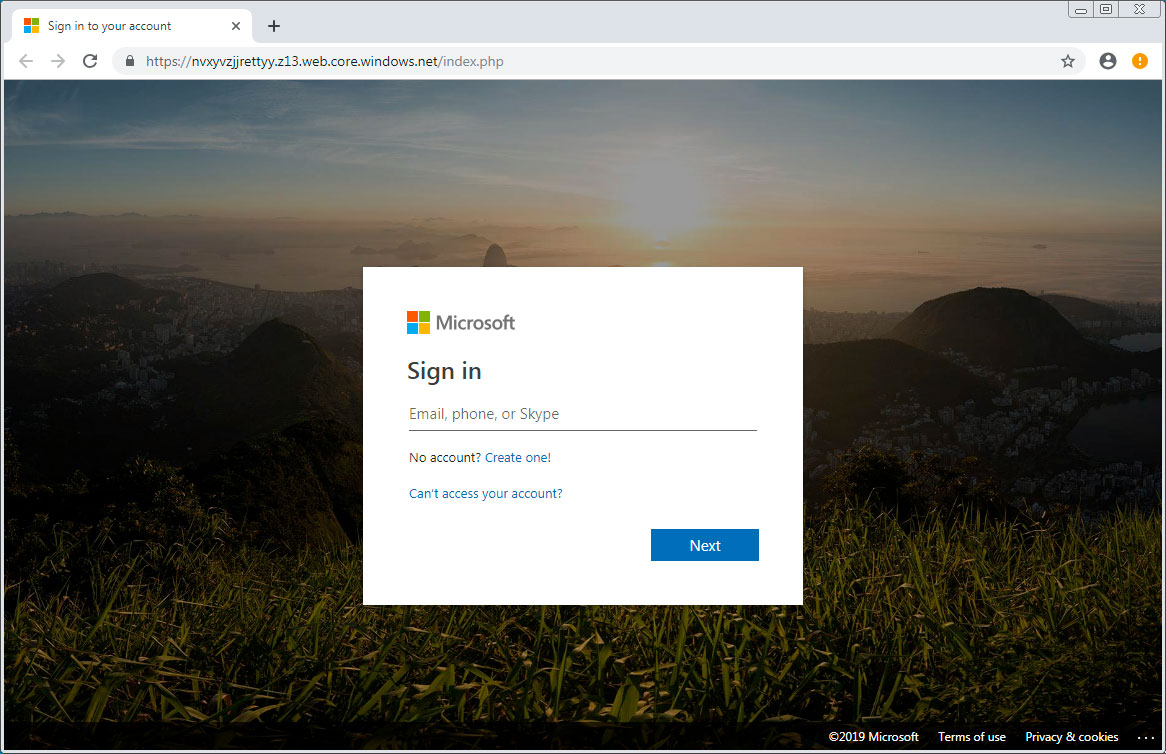
It’s the perfect recipe for tricking IT Pros into giving up admin credentials. And once the keys to the kingdom are stolen, every user account and bit of data is up for grabs.
There are two steps IT needs to take to thwart attacks like this:
1) Multi-Factor Authentication – in this specific case, the scammers had no mechanism for a second-factor pass through. But we have seen cases like this where codes sent to mobile devices are passed through to cloud applications to give attackers access. Use of multiple factors beyond just SMS messaging, etc. should be in play for every IT pro with elevated access.
2) Security Awareness Training – Even members of IT need to go through Security Awareness Training so they are practicing what they preach.Usually, it’s poor wording or HTML that gives away a phishing email, but attackers are getting better at their craft and IT shouldn’t assume they’ll always be able to spot the bad guys.
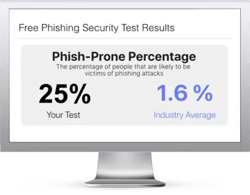
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before the bad guys do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
 Here's how it works:
Here's how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://www.knowbe4.com/phishing-security-test-offer





