
These latest attacks are designed to proxy login requests that incorporate SMS-based authentication as a way to seamlessly
bypass 2FA protection without being noticed.
Google researchers are seeing more
phishing attacks that are 2FA-aware. Attackers are realizing more organizations are embracing two-factor authentication (2FA) as a means of thwarting phishing attacks seeking to compromise credentials. By using a second authentication factor (which usually is a SMS-based verification code), attackers who only capture usernames and passwords have little use for the details collected.
According to a
recent talk with Gmail security engineering lead, Nicolas Lidzborski, cybercriminals are evolving the art of the credential phish, and are adding in mechanisms to capture and instantly use the combination of username, password, and verification code. In essence, the bad guys have come to realize SMS-based verification will be a part of the process, and have painstakingly built detailed lookalike login pages that not only accept user credentials, but also facilitate making the Google request to provide the second authentication factor.
As the victim provides the details, the malicious webpage simultaneously logs on to gain access to a users entire G Suite.
Today, it’s Google. Tomorrow, you can expect attackers to attempt this on every 2FA platform that uses some kind of single sign-on.
This is a tough attack method to crack. The pages look identical. The process looks identical. So, the only thing that would stand out is the potentially abnormal email request to view something in the user’s Google account.
Users should be educated to be mindful of emails that take them to any kind of logon page on the web. Just because they are prompted to authenticate, doesn’t mean they just blindly should. Ongoing Security Awareness Training can help users stay current with attack trends, methods, and techniques used, empowering them to know when they see something that just isn’t right, and how to avoid falling for even the most realistic scams that capture 2FA.
 These latest attacks are designed to proxy login requests that incorporate SMS-based authentication as a way to seamlessly bypass 2FA protection without being noticed.
These latest attacks are designed to proxy login requests that incorporate SMS-based authentication as a way to seamlessly bypass 2FA protection without being noticed.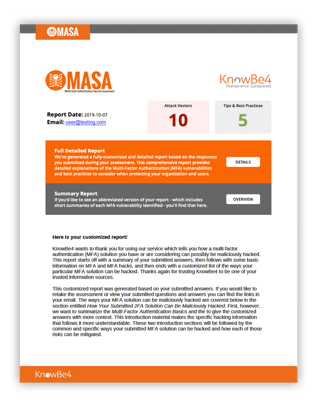 Here's how MASA works:
Here's how MASA works:




