Earlier this year we posted about Jsocket, a highly malicious Trojan that we spotted being delivered through phishing emails shared with us via the Phish Alert Button (PAB).
Although ransomware has been grabbing the majority of security-related headlines, malicious RATs and Trojans like Jsocket (and its evil cousins Adwind and AlienSpy) remain an important part of the online threat landscape, allowing malicious actors to monetize compromised systems and networks in a variety of ways.
Today we need to warn you about a new version of a very dangerous Trojan called, appropriately enough, iSpy. Unfortunately, you won't find this iSpy nearly as entertaining as the much-loved sixties TV program of the same name.
Threat researchers at Zscaler recently came across a new version of this Trojan keylogger via the company's cloud-based sandbox. You can read their full, technically detailed report here. What follows is a short summary of iSpy's main features and the threat it poses to your network.
Trojan-as-a-Service
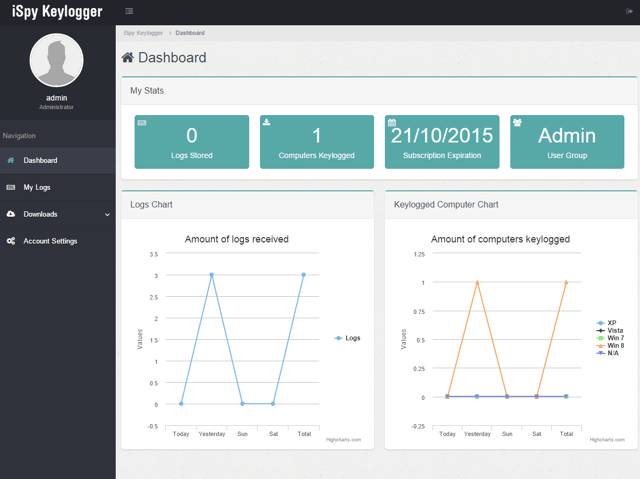
Zscaler is classifying iSpy as a commercial keylogger, though its features go well beyond those found in a simple, standard keystroke logging application. Written in .NET 2.0., iSpy is sold on underground forums through a subscription model at prices ranging as low as $25.00 per month for a version with a somewhat limited feature set. Customers are provided with a slick web panel to monitor their remotely deployed iSpy Trojan keyloggers:
Delivered via phishing with malicous attachments
iSpy is typically delivered to employee workstations via phishing emails with malicious attachments -- either zipped .JS files or macro-laden Word documents, both standard vehicles for modern email-borne threats of all kinds, including ransomware. The .JS files and Office macros function as Trojan downloaders, pulling down the full keylogger payload, which is custom-packed and may be signed with a number of different digital certificates.
Kills antivirus software on the workstation
This Trojan keylogger configures itself to auto-start with the compromised machine through a protected Autorun Registry key/value. It has the ability to kill many standard anti-virus programs as well defeat anti-malware software through other sophisticated techniques. This malicious software can also block web sites -- a feature potentially useful for preventing updates to anti-malware programs or attempts to download other detection and remediation tools.
Full-featured, dangerous capabilities
The full-featured version of iSpy comes armed with a number of dangerous capabilities including:
- keylogging
- credentials theft
- screenshot generation
- webcam monitoring
- clipboard monitoring
- file downloading
Stolen data of all kinds can be exfiltrated to C&C servers via the FTP, SMTP, and HTTP protocols. Most of the listed functionality is fairly standard for a Trojan keylogger of this kind, as it allows these criminals to monetize compromised machines and networks through a variety of means.
And, as we noted in a blog post last month, this kind of functionality is increasingly being used by ransomware developers to allow price discrimination, enabling the bad guys to tailor ransom demands to the target's ability and willingness to pay -- one factor in the rising price of ransom demands for compromised organizations.
But this new version of iSpy also steals your software licenses. What?
It's downright disconcerting that iSpy also facilitates software license theft from compromised organizations. According to Zscaler, iSpy: "contains code to steal the license keys of application software, such as Adobe Photoshop, Microsoft Office, and others. It also collects saved passwords from web browsers, email clients (such as Outlook), FTP clients (like FileZilla and CoreFTP), and games like Minecraft."
Ripped off software license information is fenced on underground forums and through other dark web venues. Imagine getting a call from Microsoft that you are in violation of your license agreements with a 200% overage. Dang!
Conclusion
Six months ago when we told you about the Jsocket Trojan, this kind of sophisticated malware is not reliably detected or stopped by your standard endpoint AV programs. Not only do Jsocket and iSpy contain AV-killing functionality, but they use a SaaS model to empower a ton of other internet criminals to spread custom-built, custom-wrapped, and custom-signed versions via specifically tailored phishing campaigns.
As a result, your employees could very well find phishing emails with an iSpy payload in their inbox, despite the presence of anti-virus applications on their desktops or Exchange security solutions running on your network. And when that happens, you need employees who have been trained to recognize dangerous phishing emails and the malicious attachments they deliver on sight.
In this situation your employees truly are your last line of defense. You can read more about this new version of iSpy in these news articles:
iSpy Keylogger Targets Passwords, Skype, Webcams
iSpy, a new sophisticated commercial keylogger in the criminal underground
iSpy Keylogger Returns with New Version and New Attacks
Free Phishing Security Test
Did you know that 91% of successful data breaches started with a spear-phishing attack?
Cyber-attacks are rapidly getting more sophisticated. We help you train your employees to better manage the urgent IT security problems of social engineering, spear-phishing and ransomware attacks. Take the first step now. Find out what percentage of your employees are Phish-prone™ with our free test. Did you know that KnowBe4 also supports "Vishing" where you can actually send your users simulated voice mail attacks?
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://www.knowbe4.com/phishing-security-test-offer





