 Ever heard: "If it was easy, everyone would do it" ?
Ever heard: "If it was easy, everyone would do it" ?
Creating a better security culture in your organization has a few challenges. Let's have a look at them, see how you can overcome some, and turn a few others around into your advantage.
The ultimate goal is your organization being such a hard target that the bad guys just get discouraged and move on.
Of course, every organization has an existing security culture. If they say they don't, they probably are reluctant to admit they have a bad security culture.
Corporate culture in general could be called the combination of all technology, knowledge, morals and even wisdom afloat in your organization.
Ever heard the statement about the difference between morals and ethics? Morals is what you do when other people are watching. Ethics is what you do when no one is watching.
You could define "Security Culture" as what happens with security when people are not being watched, are they making smart security decisions? And how do you measure it?
OK, so how do we get there?
By first having a look at the current state of affairs and see where we need to start. Here are the 5 main issues:
- Employees are not easy to train in secure behavior. They have been living their online lives for a long time, and "making smart security decisions" has not been their modus operandi. They need to be trained out of bad habits.
- Organizations do not realize the scale of the social engineering threat. Your board, C-levels, and the general employee population simply have not been aware of the massive increase of cybercrime and their tactics. Security culture is only starting to catch up with the threat landscape.
- There is no budget set aside and not enough resources allocated. It's the logical result of not realizing the threat in point 2.
- Changing a culture requires a lot of (internal) marketing and PR. Those are not areas that IT pros are trained in themselves. Creating a multi-disciplinary team that covers these skill sets is a must, but hard to do.
- Creating and maintaining an intentional Security Culture takes buy-in and work at all levels of the organization. Culture is less about words and more about actions. Creating and sustaining the culture that you want is an ongoing, intentional process. The desired cultural tones, standards, and practices must be set, modeled and evangelized at the leadership level, as well as middle-management and by influential individual contributors. Culture is set by social norms and social pressures; our job is to help shape and sustain them.
Let's have a look at these points
1: Employees are not easy to train in secure behavior.
Your employee generally operates with the concept that IT security is the responsibility of IT and not their own.
They have a "the antivirus and the firewall will keep me safe" mindset. And who can blame them, this is what they have been taught in the past. We now need to change that around and effectively communicate that is not the actual case anymore, and that security is something that belongs to each and every employee.
Training people out of bad habits is double work, they first need to "unlearn" what they have been doing and only then the right behavior can be grooved in.
However, you will find that when you explain the risk and the importance, and then train them really well in this area, they will appreciate the time and effort because it also helps them to keep their family stay safe online.
2: Organizations do not realize the scale of the social engineering threat.
It has only slowly penetrated that 91% of data breaches started with a successful phishing attack. This is now more or less an accepted fact. However, there is still a frame of mind to think that the problem will be solved with better technology, i.e. filters in the email stream.
Nothing is further from the truth. A recent report from a company that filters billions of email messages per day shows an average 10.5% miss-rate over all commerical email filters missing spam, phishing and malware attachments. C-level executives have not understood the fact that software security is hopelessly broken and that you urgently need to reinforce your human firewall.
3. There is no budget set aside and not enough resources allocated.
Not fully understanding the actual threat landscape where bad guys target and "hack the human" with social engineering causes misalignment of budget allocation. Simply put, they do not spend the budget where they get the best ROI. However, there is a ray of sunshine in this otherwise gloomy outlook.
KnowBe4 recently commissioned Forrester to conduct a Total Economic Impact™ (TEI) study, examining the potential Return on Investment (ROI) enterprises might realize by implementing the KnowBe4 Security Awareness Training and Simulated Phishing Platform. The resulting research paper assesses the performance of the KnowBe4 Platform. How does 127% ROI with a one-month payback sound?
4. Changing a culture requires a lot of (internal) marketing and PR.
The CISO should, with the full support of top leadership, oversee an organizationwide effort to step up security awareness activities. Training materials should be relatable, direct and relevant to enact a gradual shift toward a strong security culture with reminders, fresh ideas, games and, yes, the dreaded phishing test.
This transition will not happen overnight, and there will be some pushback. But the days of writing passwords on sticky notes, sharing login credentials with office staff and practicing overall poor cyber hygiene, both at work and at home, need to end. CISOs should join forces with awareness evangelists to constantly remind staff members to follow security best practices.
And, finally, point 5, defining and sustaining your culture.
We use the word ‘culture’ intentionally. Culture is shaped and reshaped by the words people say, the values that they hold (and show), and the support that they provide each member of the organization. This means that cultural ‘disjoints’ can cause dramatic problems. For example, if the organization is putting forth the message that certain principles are valued, but a subgroup of the organization doesn’t actively support or demonstrate those values, we end up with a culture that is pulling against itself.
Because of this, it is crucial to ensure that there is buy-in for each security-related value that you want to cultivate. Part of this can be accomplished and sustained through the creation of a security champion/liaison program that is intended to be an open line of mutual communication and support between key security stakeholders and other lines throughout the organization. This not only helps disseminate security-related information, but is also a mechanism for creating open dialog related to security concerns, misunderstandings, and so on. Key to this concept is having membership from the executive team, middle-management, and influential and knowledgeable individual contributors -- creating cultural reinforcement points at all levels of the organization.
So, How To Get Started?
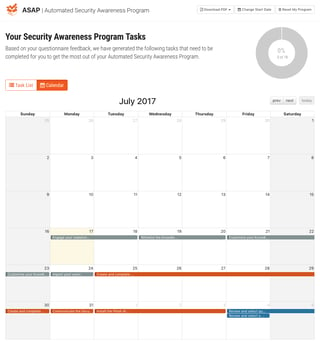
IT pros don’t exactly know where to start when it comes to creating a security awareness program that will work for their organization. We’ve taken away all the guesswork with our new Automated Security Awareness Program (ASAP).
Includes:
- 15-25 questions depending upon answers
- Suggested training materials based on answers
- Choose and change your program start date and tasks
- Calendar and list view of tasks
- Dashboard with program status, % complete, tasks overdue, etc.
- Detailed and summary exportable PDF versions of your program
- Fully mature awareness program ready in 10 minutes
If you do not have a KnowBe4 account yet, (free or paid) find out what YOUR program will look like. There is no cost… Start ASAP!
Don't like to click on redirected buttons? Cut & paste this link in your browser:
PS: If you’re a current KnowBe4 customer, just login to your console, click on ASAP at the top right and get started!





