Technically, LockerGoga is just another ransomware strain and not even a very good one. It's got bugs and it's slow. However, the gang behind it represents a dangerous combination of aggressive disruption and high-stakes targets.
Since the beginning of 2019, the LockerGoga gang has focused on industrial and manufacturing firms: French engineering consulting firm Altran, Norwegian aluminum manufacturer Norsk Hydro, and a few days ago chemical companies, Hexion and Momentive. And those are only the ones in the news as there are quite a few more.
How They Are Getting In
It's not clear yet how the LockerGoga gang gains initial access, but they seem to already know targets' credentials at the start of an intrusion, perhaps thanks to phishing attacks or by simply buying exposed RDP creds on the dark web. Once they have an initial foothold, they use the common hacking toolkits Metasploit and Cobalt Strike to move to other computers on the network and also exploit the program Mimikatz, which can pull traces of passwords out of the memory of Windows machines and allow them to gain access to more privileged accounts.
After they obtain domain admin credentials, they use Active Directory management tools to roll out their malicious payload to target machines across your network. The code is signed with stolen certificates that make it look more legitimate. And before running their encryption code, the hackers use a "task kill" command on target machines to disable their antivirus. Both of those measures have made antivirus particularly ineffective. Finally, the hackers plant a readme file on the machine that lists their demands.
In The Latest Version They Disable The Network Adapter
In the latest version of the malware that researchers have analyzed, LockerGoga goes further still: It also disables the computer's network adapter to disconnect it from the network, changes the user and admin passwords on the computer, and logs the machine off.
That's a very different approach from typical ransomware that merely encrypts some files on a machine but otherwise leaves it running, says Earl Carter, a researcher at Cisco's Talos division. The degree of disruption is counterproductive even for the hackers, since they're less likely to be paid, he argues. "Everyone is kicked off the system so they can’t even get back to look at the ransom note," he says. "It throws everything into chaos. You’ve just destroyed the operation of the system, so users can’t do anything at all, which is a much more significant impact on the network" than a typical ransomware attack. Full story at WIRED.
Five Things You Can Do About This Right Away:
- When is the last time you tested the restore function of your backups? You want to do that ASAP, and make sure you have weapons-grade backups at all times.
- Scan your network to identify any open RDP ports and ideally disable RDP completely on all Windows machines if possible. By default, the server listens on TCP port 3389 and UDP port 3389.
- Best practice to protect a network from a brute force RDP attack is to apply strong RDP security settings, including limiting or disabling access to shared folders and clipboards from remote locations.
- An RDP brute force approach does open the attacker’s information to the targeted network, so automate the process of parsing the Windows Event Viewer logs, find any compromised user accounts, identify the IP address of the attacker and block that.
- Do a no-charge Phishing Security Test and find out what percentage of your users is Phish-prone. Use that percentage as a catalyst to start a new-school security awareness training program, which—by survey—your users are actually going to appreciate because it helps them stay safe on the internet at the house. PS, the password is "homecourse". It's free.
Brand-New Ransomware Simulator Tool Now with Cryptomining Scenario
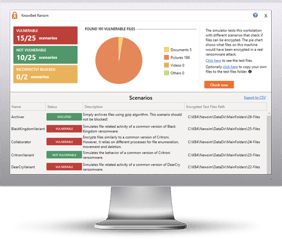
Bad guys are constantly coming out with new malware versions to evade detection. That’s why we’ve updated our Ransomware Simulated tool “RanSim” to include a new cryptomining scenario!
This new cryptomining scenario simulates a Monero cryptocurrency-mining operation on the local machine. Monero mining is the most popular cryptocurrency mined by real-world malware and takes a lot of CPU and GPU cycles to process the data necessary to generate the currencies.
Try KnowBe4’s NEW Ransomware Simulator tool and get a quick look at the effectiveness of your existing network protection against the latest threats.
RanSim will simulate 13 ransomware infection scenarios and 1 cryptomining infection scenario to show you if a workstation is vulnerable to infection.
Here's how RanSim works:
- 100% harmless simulation of real ransomware and cryptomining infection scenarios
- Does not use any of your own files
- Tests 14 different types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
This is a complementary tool and will take you 5 minutes max. RanSim may give you some insights about your endpoint security you never expected!
Don't like to click on redirected buttons? Copy and paste this link into your browser:
https://info.knowbe4.com/ransomware-simulator-tool-1