Officials in Jackson County, Georgia, paid $400,000 to cyber-criminals this week to get rid of a ransomware infection and regain access to their IT systems. The County hired cyber-security consultant to negotiate ransom fee with hacker group. Jackson County officials have not yet confirmed how hackers breached their network.
Officials in Jackson County, Georgia, paid $400,000 to cyber-criminals this week to get rid of a ransomware infection and regain access to their IT systems. The County hired cyber-security consultant to negotiate ransom fee with hacker group. Jackson County officials have not yet confirmed how hackers breached their network.
The infection forced most of the local government's IT systems offline, with the exception of its website and 911 emergency system.
"Everything we have is down," Sheriff Janis Mangum told StateScoop in an interview. "We are doing our bookings the way we used to do it before computers. We're operating by paper in terms of reports and arrest bookings. We've continued to function. It's just more difficult."
Jackson County officials notified the FBI and hired a cyber-security consultant. The consultant negotiated with the ransomware operators, and earlier this week the Georgia county paid $400,000 to hackers to get a decryption key and regain access to their ransomed files.
County officials are in the process of decrypting affected computers and servers, Jackson County Manager Kevin Poe told Online Athens in an interview.
"We had to make a determination on whether to pay," Poe said. "We could have literally been down months and months and spent as much or more money trying to get our system rebuilt."
Poe identified the ransomware that infected the county's network as "Ryuk" a well-known ransomware strain that is currently undecryptable.
It looks like there are two Ryuk gangs at the moment, one out of North Korea and the other one is believed to be operating out of Eastern Europe. For the past year, both have focused on targeting local government, healthcare, and large enterprise networks. They intentionally go after big targets as part of a tactic known as "big game hunting."
Ryuk ransomware is usually deployed on networks following brute force RDP attacks or phishing infections with Emotet or Trickbot malware.
Jackson County won't be the victim who paid the largest ever ransom demand, though. This "honor" goes to South Korean web hosting firm Internet Nayana, which paid 1.3 billion won ($1.14 million) worth of bitcoins to a hacker following a ransomware attack in June 2017. More at ZDNet.
How Vulnerable Is Your Network When An APT Has Penetrated Your Systems?
Want to find out if your endpoint security software will block ransomware strains like Ryuk?
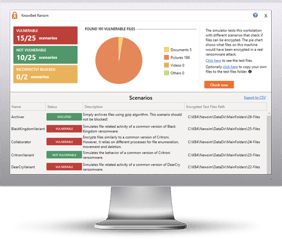
Bad guys are constantly coming out with new malware versions to evade detection. That’s why we’ve updated our Ransomware Simulated tool “RanSim” to include a new cryptomining scenario!
This new cryptomining scenario simulates a Monero cryptocurrency-mining operation on the local machine. Monero mining is the most popular cryptocurrency mined by real-world malware and takes a lot of CPU and GPU cycles to process the data necessary to generate the currencies.
Try KnowBe4’s NEW Ransomware Simulator tool and get a quick look at the effectiveness of your existing network protection against the latest threats.
RanSim will simulate 13 ransomware infection scenarios and 1 cryptomining infection scenario to show you if a workstation is vulnerable to infection.
Here's how RanSim works:
- 100% harmless simulation of real ransomware and cryptomining infection scenarios
- Does not use any of your own files
- Tests 14 different types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
This is a complementary tool and will take you 5 minutes max. RanSim may give you some insights about your endpoint security you never expected!
Don't like to click on redirected buttons? Copy and paste this link into your browser:
https://info.knowbe4.com/ransomware-simulator-tool-1
Image credits: Check Point