 Cybercriminals know that targeted social engineering attacks lead to the highest payoffs, so the frequency and sophistication of these attacks is guaranteed to increase, writes Jasmine Henry at IBM Security Intelligence. Henry lays out four rising social engineering attacks that organizations need to be aware of.
Cybercriminals know that targeted social engineering attacks lead to the highest payoffs, so the frequency and sophistication of these attacks is guaranteed to increase, writes Jasmine Henry at IBM Security Intelligence. Henry lays out four rising social engineering attacks that organizations need to be aware of.
Business Email Compromise
The first type of attack is business email compromise (BEC, also known as CEO fraud), which involves compromising an email account or spoofing an email address to trick employees into transferring money or granting access to an attacker. Henry says that if an organization doesn’t have proper security measures, these attacks “can be both easy and highly rewarding for cybercriminals.”
Whaling
A variant of BEC is whaling, in which attackers impersonate an executive at an organization to gain maximum leverage when they make their demands. These attacks are less frequent since there are fewer potential targets, but they cause far more damage than most attacks.
Extortion Attempts
Extortion attempts are also growing more frequent. The vast majority of these attempts are pure scams, such as widespread sextortion campaigns. However, attackers do sometimes steal sensitive data and threaten to release it unless the victim pays a ransom. Henry points to a newer spin on this type of extortion in which criminals utilize crowdfunding to raise money before they release the information, allowing attackers to get paid even if the victim doesn’t give in.
Pretexting
A fourth rising threat is pretexting, where an attacker poses as a trusted party and builds rapport with someone inside of an organization. Once they’ve gained an employee’s trust, they’ll trick the target into doing something that compromises the organization’s security.
Henry concludes that organizations need to take a new approach in order to fight these threats.
“Although security awareness training remains a critical protection against the highest-volume forms of social engineering attacks, it’s time for organizations to look beyond basic user awareness,” she writes. “Some of today’s most profitable attacks involve criminal methodologies that aren’t visible to the bare eye. Inadvertent insiders are the weakest link in any organization, and it’s more important than ever to involve a comprehensive plan for cyber resilience, including simulation training and a strong resiliency plan.”
The damage caused by social engineering depends on the scenario and the organization. Any of these four types can cause massive damage to an organization's reputation, stock price or direct cash losses in the case of ransom paid due to a ransomware infection.
New-school security awareness training with simulated social engineering attacks can enable your employees to detect suspicious activity while following policies that prevent attackers from exploiting weaknesses in human communication.
Security Intelligence has the story: https://securityintelligence.com/articles/4-social-engineering-threats-to-keep-an-eye-on-and-how-to-stop-them/
Will your users respond to social engineering attacks?
KnowBe4's new Phishing Reply Test (PRT) is a complimentary IT security tool that makes it easy for you to check to see if key users in your organization will reply to a highly targeted attack without clicking on a link. PRT will give you quick insights into how many users will take the bait so you can take action to train your users and better protect your organization from these fraudulent attacks!
 Here's how the Phishing Reply Test works:
Here's how the Phishing Reply Test works:
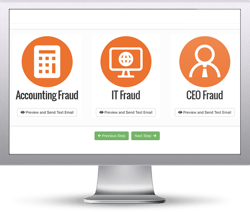
- Immediately start your test with your choice of three phishing email reply scenarios
- Spoof a Sender’s name and email address your users know and trust
- Phishes for user replies and returns the results to you within minutes
- Get a PDF emailed to you within 24 hours with the percentage of users that replied
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://www.knowbe4.com/phishing-reply-test





