 The Belgian Crelan Bank was the victim of a 70 million euro (75.8M U.S.) fraud that was launched from another country. They claim this CEO Fraud was discovered during an internal audit and does not affect their viability.
The Belgian Crelan Bank was the victim of a 70 million euro (75.8M U.S.) fraud that was launched from another country. They claim this CEO Fraud was discovered during an internal audit and does not affect their viability.
The bank said: "As a result of these facts, we took additional, exceptional measures to strengthen our internal security procedures. We informed the justice department and we are investigating this incident. Existing customers are not impacted."
Luc Versele, CEO of Crelan was quoted: “Looking at our historic reserves, Crelan can shoulder this fraud without any negative impact for our customers and affiliates. We are still viable and our total capital is 1,1 Billion Euro."
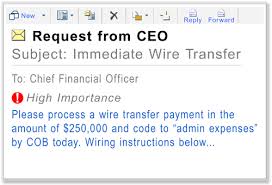 CEO Fraud, also called Business Email Compromise, is the next cybercrime wave, as per the FBI who recently warned that this has cost small- and medium enterprise 1.2 billion dollars in damages between October 2013 and August 2015. C-level employees, especially CEOs and CFOs, have to be aware of the various techniques the scammers are using to trick them into wiring out large amounts of money.
CEO Fraud, also called Business Email Compromise, is the next cybercrime wave, as per the FBI who recently warned that this has cost small- and medium enterprise 1.2 billion dollars in damages between October 2013 and August 2015. C-level employees, especially CEOs and CFOs, have to be aware of the various techniques the scammers are using to trick them into wiring out large amounts of money.
Most small and medium enterprises do not know that they are not FDIC-insured like consumers, and that their cyber security insurance (if they even have it) also may not cover this specific type of fraud, because no IT infrastructure was compromised.
What you can do about it:
- Alert your execs. These scams are getting more sophisticated by the month and be on the lookout
- Review your Wire Transfer security policies and procedures
- Learn about Social Engineering red flags
Obviously all your employees need to be stepped through effective security awareness training to prevent social engineering attacks like this from getting through.




