 In the quest to create a more secure environment, new ways to authenticate that replace the password are being sought. But it’s looking like passwords are here to stay.
In the quest to create a more secure environment, new ways to authenticate that replace the password are being sought. But it’s looking like passwords are here to stay.
The simple password has been used as a means to identify an individual for as long as any of us can remember. For decades, it served as the secret phrase that only its owner knew. But as technology has evolved, the password has become less secure; users are sharing them far too often, they are the target of attacks, and users are being fooled into giving them up.
Because of this, some organizations are looking to biometrics as a replacement for passwords. Take the use of fingerprints or facial recognition on smartphones as ways to access applications, data, and devices, for example.
While biometrics is recognized as a potential additional authentication factor, even according to the National Institute for of Standards and Technology (NIST), “biometrics, when employed as a single factor of authentication, do not constitute acceptable secrets for digital authentication,” noting, “but they do have their place in the authentication of digital identities.”
In a recent article, Gerald Beuchelt, CISO at LogMeIn discussed 5 reasons why biometrics can’t be considered as a replacement for passwords. Two of the more critical reasons include:
- You can’t update biometrics – should your password be compromised, just change it. But if your biometric data is stolen and replicated, you can’t get a new face, right?
- Higher risk requires multiple authentication factors – Biometrics alone, like passwords, still don’t provide enough authentication assurance that it’s really you. As previously pointed out, even NIST sees value in biometrics, but as a part of a larger authentication strategy.
Organizations looking to enhance their security stance around authentication should be looking employ two-factor authentication (2FA) at a minimum, and for high-risk environments multiple-factor authentication (MFA). Depending on your security requirements and available technology, biometrics may have a place.
It’s just not going to be replacing passwords anytime soon. And that puts organizations without 2FA or MFA at risk of attacks focused on compromising credentials. Users need to be taught to be watchful for attacks using Security Awareness Training to that they can spot social engineering and phishing attacks targeting passwords.
How vulnerable is your network to hacked user passwords?
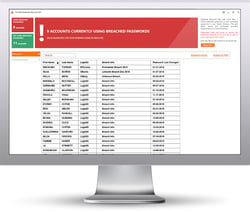
25% of employees use the same password for all logins. What if that password is available on the dark web? A massive amount of passwords are compromised due to data breaches and used by the bad guys for attacks. KnowBe4’s free Breached Password Test (BPT) checks to see if your users are currently using passwords that are in publicly available breaches associated with your domain. BPT checks against your Active Directory and reports compromised passwords in use right now so that you can take action immediately!
 Here's how it works:
Here's how it works:
- Checks to see if your company domains have been part of a data breach that included passwords
- Checks to see if any of those breached passwords are currently in use in your Active Directory
- Does not show/report on the actual passwords of accounts
- Just download the install and run it
- Results in a few minutes!
Find out now which users are using hacked passwords!
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://www.knowbe4.com/breached-password-test





