 Cybercriminals thrive on misuse of credentials, and users sharing them only makes the criminal’s job easier. The latest report from LastPass shows password sharing is rampant.
Cybercriminals thrive on misuse of credentials, and users sharing them only makes the criminal’s job easier. The latest report from LastPass shows password sharing is rampant.
The password has been the long-standing guardian keeping unauthorized users from accessing data, applications, and systems they shouldn’t. But, the password is only powerful when the assigned user keeps it private. But, according to LastPass’ 2018 State of the Password report, the average employee shares six (yes, SIX) passwords – and increase of 33% from last year’s number of only 4 passwords!
While 45% of businesses state they are using multi-factor authentication (MFA), the ability to share multiple passwords indicates a few possibilities:
- Not all users are using MFA
- Not all applications are tied into MFA
In either case, the end result is only a portion of production (that is, the mix of users and applications) is protected by MFA. Now, add to that the fact that the use of stolen credentials is the number one threat action in a data breach, and you begin to realize how much cybercriminals LOVE the news around rampant password sharing. It’s a dangerous cocktail that tastes like a successful attack.
Users need to be taught via Security Awareness Training the need for a security culture within the organization, why password sharing is bad, and how to spot social engineering scams to avoid becoming a victim. Ongoing training will elevate the employee’s intrinsic sense of the need for security in all they do, lowering the risk of successful attack.
How vulnerable is your network to hacked user passwords?
 A whopping 25% of employees are using the same password for all logins. What if that password is available on the dark web? A massive amount of passwords are compromised due to data breaches and used by the bad guys for attacks. Are any hacked passwords in use within your organization?
A whopping 25% of employees are using the same password for all logins. What if that password is available on the dark web? A massive amount of passwords are compromised due to data breaches and used by the bad guys for attacks. Are any hacked passwords in use within your organization?
Using breached passwords puts your network at risk. Password policies often do not prevent employees using known bad passwords. Making your users frequently change their passwords isn’t a good solution either. It only takes one compromised password match for the bad guys to gain access.
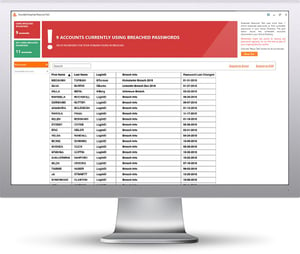
KnowBe4’s free NEW Breached Password Test (BPT) checks to see if your users are currently using passwords that are in publicly available breaches associated with your domain. BPT checks against your Active Directory and reports compromised passwords in use right now so that you can take action immediately!
Here's how Breached Password Test works:
![]() Checks to see if your company domains have been part of a data breach that included passwords
Checks to see if your company domains have been part of a data breach that included passwords
![]() Checks to see if any of those breached passwords are currently in use in your Active Directory
Checks to see if any of those breached passwords are currently in use in your Active Directory
![]() Does not show/report on the actual passwords of accounts
Does not show/report on the actual passwords of accounts
![]() Just download the install and run it
Just download the install and run it
![]() Results in a few minutes!
Results in a few minutes!
Find out now which users are using hacked passwords!
https://www.knowbe4.com/breached-password-test
Requirements: Active Directory, Windows 7 or higher (32 or 64bit) NOTE: the analysis is done on the workstation you install BPT on, no confidential data leaves your network, and actual passwords are never disclosed.




