 The king of callback phishing campaigns has evolved their methods to include better phishing emails, phone call scams, and final payloads to ensure they achieve their malicious goals.
The king of callback phishing campaigns has evolved their methods to include better phishing emails, phone call scams, and final payloads to ensure they achieve their malicious goals.
The BazarCall phishing technique – named after the most common payload used in the scam, BazarLoader, as well as the use of phone calls as the medium to trick victims into downloading – has been around for a few months. Seen initially used to deliver Conti ransomware, this methodology has been used by other cybercriminal groups.
According to a new report from security researchers at Trellix, more BazarCall scams are showing up in the wild. In each case, an invoice or notification of a processed payment is sent – used to grab the attention of the victim and create a sense of urgency to respond. As you can see below, the scammers go to some relatively decent lengths to ensure their phishing emails look legitimate.
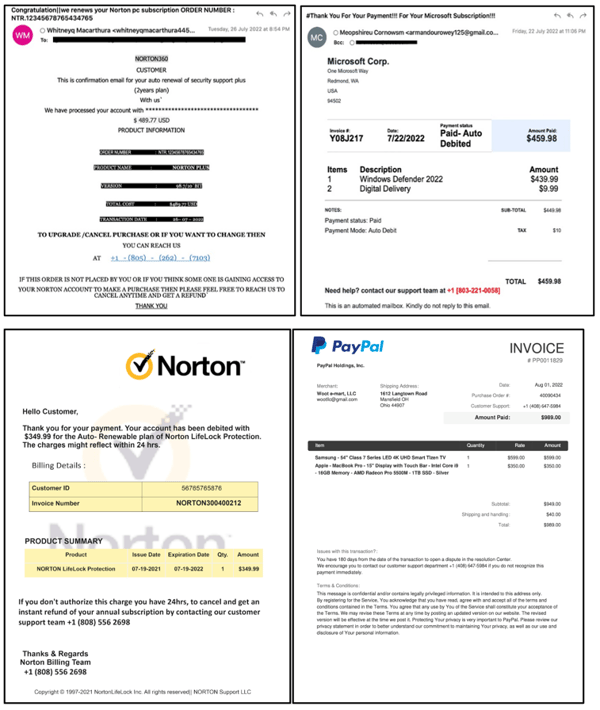
Source: Trellix
As part of their campaign, note that there are no email addresses available to respond to. Instead, a phone number is prominently displayed at the bottom of each email, giving the victim only one option to attempt to “address” the undesired expense.
The scammer on the other end of the call uses one of a few patterned call scripts to convince the victim they need to allow the scammer to take over the victim’s computer using support software. Legitimate-looking websites are used to further establish legitimacy:
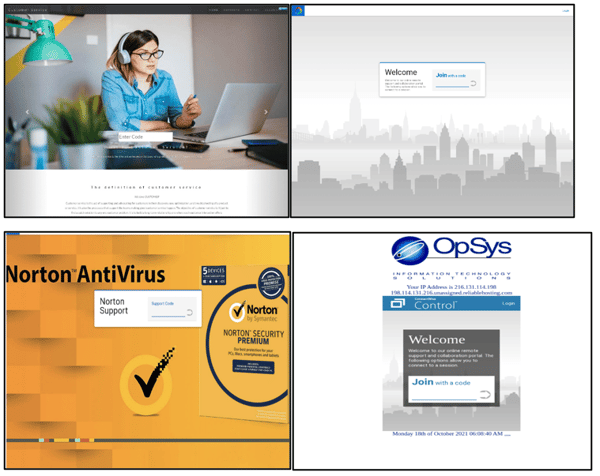
Source: Trellix
The real scam comes into play where the victim is convinced to log onto their bank’s website, where the scammer initiates are transfer of funds through locking and unlocking the victim’s screen while performing the malicious act.




