 The headline alone sounds the warning that ransomware gangs aren’t just threatening to release exfiltrated data; they’re full out retaliating when they don’t get their ransoms paid.
The headline alone sounds the warning that ransomware gangs aren’t just threatening to release exfiltrated data; they’re full out retaliating when they don’t get their ransoms paid.
I wrote recently about the Ragnar Locker ransomware attack on Taiwanese Chip manufacturer, ADATA. Early reports indicated that 1.5TB of data may have been stolen. But after ADATA reportedly was able to recover operations without paying the ransom, the ransomware gang published links to 700GB of stolen data Saturday hosted on legitimate storage vendor, MEGA. While access to the links was short-lived (the Ragnar-owned account was quickly disabled), there was an opportunity to see what kinds of data was exfiltrated and published:
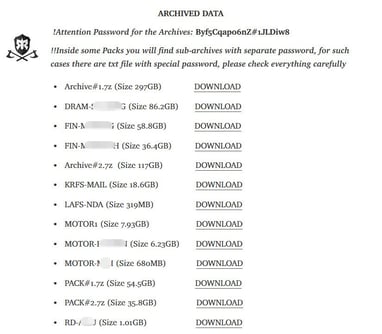
Source: ADATA
Ransomware is no joke; with 77% of ransomware attacks now include the threat to leak exfiltrated data, organizations can no longer rest on the “we have backups” line of thinking. Instead, it’s necessary to stop these attacks before they are able to access and exfiltrate your data. There are three basic stopgaps you can rest on:
- Find and secure vulnerabilities on endpoints, servers, networking devices, applications, IoT devices, and anything else that is Internet-facing.
- Stop using RDP, period. If you need some form of Internet-facing remote access, use a VPN, a SASE solution, or something of the kind.
- Implement Security Awareness Training to improve the security of your users and to reduce the likelihood of them engaging with phishing email content designed to trick them into installing malware, giving up credentials, or performing unsanctioned tasks that hurt the organization financially.
 Here's how it works:
Here's how it works:




