A recent discovery of exposed data on a web-facing server owned by data aggregator and analytics provider Apollo demonstrates how data breaches empower scammers.
Cybercriminals who choose not to take the targeted attack route need to lever millions of email addresses to realize the desired attack result. Bad guys like former “Crime-as-a-Service” businessman Peter Levashov used to sell millions of email addresses for only a few hundred dollars.
But, as a cybercriminal, if you could get your hands on over 200 million email addresses, you’d think you hit the jackpot!
Penetration Testing vendor Night Lion Security recently found 212 million records exposed to the web and promptly notified Apollo of the potential breach.

Had the exposed data been found by cybercriminals (the industry has seen instances of white hat hackers going black) and not Night Lion, the potential for scammers and fraudsters to launch phishing attacks against a massive number of email recipients would not only be possible, but probable.
Seasoned cybercriminal organizations have already done the math; knowing for every number of email recipients how many will become victims. The “gift” of 212 million would simply result in a calculated outcome.
With much of the Apollo records being so detailed they were mistook for LinkedIn data, the implication is it’s likely some of your organization’s users were in that data set.
While no breach occurred, this story is a reminder that organizations should be prepared for the next big breach by implementing Security Awareness Training to prepare users when they face phishing attacks, social engineering scams, and other attacks that put the organization at risk. There are tons of data breaches though where passwords are stolen.
Are your user’s passwords…P@ssw0rd? Verizon's Data Breach Report showed that 81% of hacking-related breaches used either stolen and/or weak passwords. Employees are the weakest link in your network security, using weak passwords and falling for phishing and social engineering attacks.
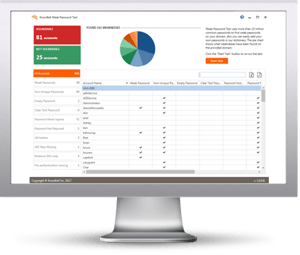
KnowBe4's Weak Password Test checks your Active Directory for 10 different types of weak password related threats and reports any fails so that you can take action.
WPT gives you a quick look at the effectiveness of your password policies and any fails so that you can take action. WPT tests against 10 types of weak password related threats for example; Weak, Duplicate, Empty, Never Expires, plus 6 more.
 Here's how Weak Password Test works:
Here's how Weak Password Test works:
![]() Reports on the accounts that are affected
Reports on the accounts that are affected
![]() Tests against 10 types of weak password related threats
Tests against 10 types of weak password related threats
![]() Does not show/report on the actual passwords of accounts
Does not show/report on the actual passwords of accounts
![]() Just download the install and run it
Just download the install and run it
![]() Results in a few minutes!
Results in a few minutes!
This will take you 5 minutes and may give you some insights you never expected. By the way, this is a free tool!
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





