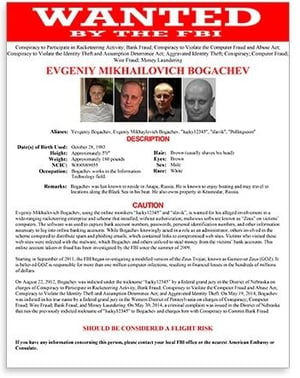
 This latest story about one specific cybercriminal group shows how even the most trusted of white-hats can give in to the lure of financial profit, following Evgeniy Bogachev who retired at the Black Sea with more than 100 million dollars in ill-gotten CryptoLocker gains.
This latest story about one specific cybercriminal group shows how even the most trusted of white-hats can give in to the lure of financial profit, following Evgeniy Bogachev who retired at the Black Sea with more than 100 million dollars in ill-gotten CryptoLocker gains.
A recent report from threat intelligence company Group-IB tells the tale of the latest cybercriminal group – Silence. The actions and expertise demonstrated by this group of only two talented Russian hackers shows the likelihood that one looks to be a current or former employee of a cybersecurity firm, and the other a seasoned penetration tester.
The evidence of this being a “white hat gone black” group is pretty solid:
- Access to non-public malware samples that are reverse engineered and crafted into unique attacks
- Their use of malware analysis and use of threat intelligence to determine their attack methods
- Customization of utilities used by other groups
- Their ability to freely navigate inside bank networks without detection
Their initial attacks in 2017 were considered “amateur”, but telltale signs of newer attacks by Silence show they have progressed to more sophisticated and successful attacks, netting them over $550K in the last year.
Now active in over 25 countries, Silence represents the speed at which good guys can go bad, as well as bad criminals becoming good at their art.
With the lines between good and bad guys blurring, the likelihood of successful attack using methods such as social engineering increases dramatically. Think about it – the guys at Silence already know what kinds of security solution you have in place (they likely work for a company that implements those very same solutions). The one part of the equation even white hat-turned black hackers can’t control is your user’s participation in a phishing scam or other social engineering attack. So, it’s important for your users to remain vigilant by staying up-to-date on the latest attack methods, scams, and techniques through Security Awareness Training.
Free Phishing Security Test
91% of successful data breaches started with a spear phishing attack
Would your users click on a phishing mail? We help you train your employees to better manage the urgent IT security problems of social engineering and phishing and attacks. Take the first step now. Find out what percentage of your employees are Phish-prone™ with our free test.
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





