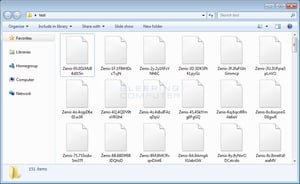
Larry Abrams at Bleepingcomputer warned against a new strain called Zenis Ransomware, which was discovered this week by the MalwareHunterTeam
"While it is currently not quite clear yet how Zenis is being distributed, it may very well get in through RDP. Multiple victims have already become infected with this ransomware. What is most disturbing about Zenis is that it not encrypts your files, but also purposely deletes your backups.
When MalwareHunterTeam found the first sample, it was utilizing a custom encryption method when encrypting files. The latest version, and the one we will discuss in this article, utilizes AES encryption to encrypt the files.
At this time there is no way to decrypt Zenis encrypted files, but Michael Gillespie is analyzing the ransomware for weaknesses. Therefore, if you are infected with Zenis, do not pay the ransom. Instead you can receive help or discuss this ransomware in our dedicated Zenis Ransomware help & support topic.
How to protect yourself from the Zenis Ransomware
In order to protect yourself from ransomware in general, it is important that you use good computing habits and security software. First and foremost, you should always have a reliable and tested backup of your data that can be restored in the case of an emergency, such as a ransomware attack.
As Zenis Ransomware may be installed via hacked Remote Desktop services, it is very important to make sure its locked down correctly. This includes making sure that no computers running remote desktop services are connected directly to the Internet. Instead place computers running remote desktop behind VPNs so that they are only accessible to those who have VPN accounts on your network.
It is also important to setup proper account lockout policies so that it makes it difficult for accounts to be brute forced over Remote Desktop Services.
You should also have security software that incorporates behavioral detections to combat ransomware and not just signature detections or heuristics. For example, Emsisoft Anti-Malware and Malwarebytes Anti-Malware both contain behavioral detection that can prevent many, if not most, ransomware infections from encrypting a computer.
Last, but not least, make sure you practice the following security habits, which in many cases are the most important steps of all:
- Backup, Backup, Backup!
- Do not open attachments if you do not know who sent them.
- Do not open attachments until you confirm that the person actually sent you them,
- Scan attachments with tools like VirusTotal.
- Make sure all Windows updates are installed as soon as they come out! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Older programs contain security vulnerabilities that are commonly exploited by malware distributors. Therefore it is important to keep them updated.
- Make sure you use have some sort of security software installed that uses behavioral detections or white list technology. White listing can be a pain to train, but if your willing to stick with it, could have the biggest payoffs.
- Use hard passwords and never reuse the same password at multiple sites.
Post with more technical detail: https://www.bleepingcomputer.com/news/security/zenis-ransomware-encrypts-your-data-and-deletes-your-backups/
Don't be a victim again. Get your Ransomware Hostage Rescue Manual.
 Get the most informative and complete hostage rescue manual on Ransomware. This 20-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with malware like this. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:
Get the most informative and complete hostage rescue manual on Ransomware. This 20-page manual is packed with actionable info that you need to prevent infections, and what to do when you are hit with malware like this. You also get a Ransomware Attack Response Checklist and Prevention Checklist. You will learn more about:
- What is Ransomware?
- Am I Infected?
- I’m Infected, Now What?
- Protecting Yourself in the Future
- Resources
Don’t be taken hostage by ransomware. Download your rescue manual now!

Or cut & paste this link in your browser: http://info.knowbe4.com/ransomware-hostage-rescue-manual-0
PS: Technically speaking, your users are the new DMZ, and you have to create a human firewall. Effective security awareness training really is a must these days. Find out how affordable this is and be pleasantly surprised.




