 In a Jan 10, 2019 article, the Wall Street Journal reconstructed the worst known hack into the USA's power grid revealing attacks on hundreds of small contractors.
In a Jan 10, 2019 article, the Wall Street Journal reconstructed the worst known hack into the USA's power grid revealing attacks on hundreds of small contractors.
The title is very apt: "America’s Electric Grid Has a Vulnerable Back Door—and Russia Walked Through It".
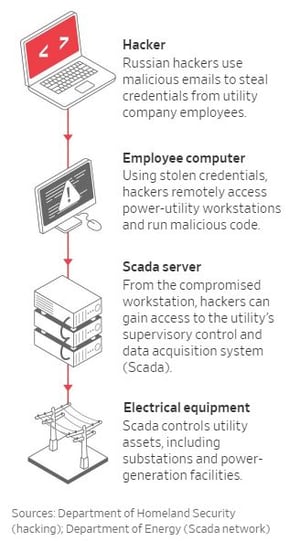
It's so relevant because it describes a very effective supply-chain attack that could happen to your own organization as well. The article focuses on the spear phishing and watering hole attacks that compromised small contractors and giving the attackers a footprint to hack further up the power grid chain. Remember the Target hack?
The Wall Street Journal pieced together this account of how the attack unfolded through documents, computer records and interviews with people at the affected companies, current and former government officials and security-industry investigators. Some experts believe two dozen or more utilities ultimately were breached.
It's a must-read because this is the No.1 vulnerability that leads to the dreaded data breach. If I were you I would sit down with your management team do the following exercise:
- Identify the top 5 suppliers that would cause downtime or serious disruption of your production if they would get hacked or were off the air
- Find out if they only require once-a-year awareness training just to be compliant
- To keep their business as your supplier, require them to sign up with KnowBe4, and deliver you the evidence that their users have stepped through the 45-minute module and get sent simulated phishing attacks once a month. As you see, I'm dead serious here.
This excellent WSJ reporting demonstrates again that your own employees need to be the strongest human firewall possible, and that your suppliers also need to be part of that same defense-in-depth strategy.
Here is the link to that article one more time, so you can cut & paste it. This may be the most important article related to InfoSec your C-levels read this year. Make sure they do:
https://www.wsj.com/articles/americas-electric-grid-has-a-vulnerable-back-doorand-russia-walked-through-it-11547137112
Let's stay safe out there.
Warm regards,Stu Sjouwerman
Founder and CEO, KnowBe4, Inc.





