.jpg?width=400&height=225&name=Evangelists-Martin%20Kraemer%20(1).jpg) In essence, that is the disclosure and notification message that the open-source developer "qix" sent to the world when he was social engineered to give up access credentials to his GitHub account.
In essence, that is the disclosure and notification message that the open-source developer "qix" sent to the world when he was social engineered to give up access credentials to his GitHub account.
Using his account, the attackers inserted malware in a series of popular NPM packages to direct cryptocurrency payments to their own wallets.
While it seems the actual financial damage was limited, as the malicious code triggered CD/CI compilation errors, two hours of the malicious code being published on GitHub would have been enough to cause significant damage to many organizations.
In this case, the payload was perhaps not well-tested, which appears to be a rookie mistake for cybercriminals. However, the damage could have been significant as several affected packages have average weekly downloads in the hundreds of millions: chalk (300M weekly downloads), debug (358M downloads), and ansi-styles (371M downloads).
The payload would have been very aggressive if deployed successfully:
- address replacements for all browser calls using fetch and XMLHttpRequest functions and thereby intercepting all network traffic to replace any crypto address with an attacker wallet
- active transaction hijacking with wallet extensions such as MetaMask to replace recipient addresses with attacker wallets leading to unwittingly approved transactions; and multi-chain support including Bitcoin, Ethereum, Solana, Tron and others.
The solution: carefully implement security safeguards into your CI/CD system. Enhanced security measures across the open-source ecosystem are urgently required, including phishing-resistant multi-factor authentication, trusted publishing mechanisms and improved monitoring of package changes.
Organizations should no longer blindly trust package managers, as any update could potentially introduce malicious code. Instead, updates must be verified and monitored to ensure a protected software ecosystem in organizations.
The developer’s initial announcement: https://bsky.app/profile/bad-at-computer.bsky.social/post/3lydioq5swk2y
Here is full technical analysis: https://socket.dev/blog/npm-author-qix-compromised-in-major-supply-chain-attack
Here is what the attack would look like in real life: https://github.com/naugtur/running-qix-malware?tab=readme-ov-file
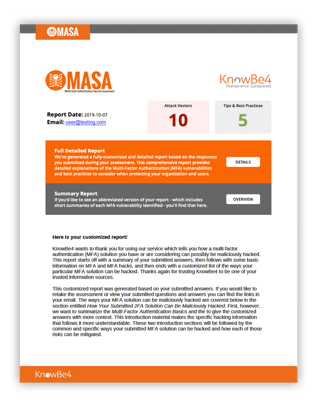 Here's how MASA works:
Here's how MASA works:




