 Clad in a blue suit and conservative necktie, KnowBe4's Chief Hacking Officer Kevin Mitnick no longer looks the part of the precocious teen who started hacking into computer systems while still in high school.
Clad in a blue suit and conservative necktie, KnowBe4's Chief Hacking Officer Kevin Mitnick no longer looks the part of the precocious teen who started hacking into computer systems while still in high school.
But when asked if any system is unhackable, there’s a youthful gleam in his eyes.
"I don’t know any system out there that’s impenetrable,” Mitnick told an audience of about 1,500 engineers at the Freescale Technology Forum (FTF) in Austin, Texas this week. “In our experience, when we are hired by clients to attack their systems, our success rate is 100%.”
Mitnick, who goes by “the world’s most famous hacker,” knows about computer vulnerabilities. His resumé is replete with conquests of 40 major corporations. He once had the dubious distinction of being on the FBI’s Most Wanted list, and spent prison time in solitary confinement because prosecutors feared he could break into NORAD computers from his cell and launch nuclear missiles.
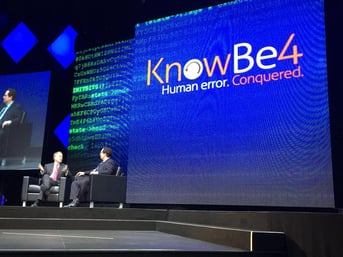
The pictures show Kevin talking about security with Freescale Semiconductor CEO Gregg Lowe.
At this week’s FTF conference, Mitnick focused on the growing influence of the Internet of Things (IoT), and the possibility of such applications being easily compromised. He suggested that the IoT has many of the same issues that now face corporate computer networks. Lack of encryption, authentication weaknesses, and password reset problems are just as likely to compromise the security of IoT applications, he said.
"Those same vulnerabilities exist in the IoT,” he said. “If I want to get information from a device, all I have to do is go out and buy one, and then extract the firmware.”

Mitnick said he used that methodology recently after his company,Mitnick Security Consulting, was hired by a well-known chain of gas stations to examine their payment security.
He first found vulnerabilities in the company’s web interfaces. Then he bought one of its payment devices over e-Bay, extracted the firmware, and easily downloaded a slew of credit and debit card numbers.
Although most businesses are more savvy about security today, the consequences can be far more dire, and the possibilities more widespread. According to a forecast from Gartner Inc. there could be as many as five billion IoT devices online in 2015, in applications ranging from industrial sensor networks to home appliances to utility control systems. And that number could grow to 20 billion by 2020, creating a huge opportunity for determined criminals.
Those facts were apparently not lost on engineers, who lined up to speak to Mitnick and get his business card after the conference’s keynote speech. "People need to know,” he explained. “The IoT is exploitable, just like any other device.”
Want to see a demo of Kevin Mitnick explaining how easy it is to get social engineered by an infected MS Word file?
This article was cross-posted from DesignNews
Related Pages: Kevin Mitnick





