 A Russian ransomware group named "Evil Corp" who was indicted by the Justice Department in December is now targeting employees working from home during the COVID-19 pandemic and attempting to get inside their networks with malware, according to Symantec.
A Russian ransomware group named "Evil Corp" who was indicted by the Justice Department in December is now targeting employees working from home during the COVID-19 pandemic and attempting to get inside their networks with malware, according to Symantec.
In an urgent warning issued Thursday night, the company reported that Russian hackers had exploited the sudden change in American work habits to inject code into corporate networks with a speed and breadth not previously witnessed.
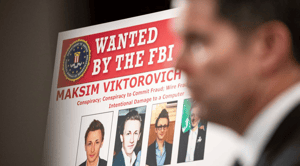
The hackers group “Evil Corp.,” is a play off the “Mr. Robot” television series. In December, the Justice Department said they had “been engaged in cybercrime on an almost unimaginable scale,” deploying malware to steal tens of millions of dollars from online banking systems. The Treasury Department placed sanctions on them, and the State Department offered $5 million for information leading to the arrest or conviction of the group’s leader.
The attack’s methodology suggests it was intended for the work-at-home era.
The malware, Mr. Chien said, was deployed on common websites and even one news site. But it did not infect every computer used to go shopping or read about the day’s events. Instead, the code looked for a sign that the computer was part of a major corporate or government network. For example, many firms have their employees use a “virtual private network,” or V.P.N., a protected channel that allows workers sitting in their basements or attics to tunnel into their corporate computer systems as if they were at the office.
“These attacks do not try to get into the V.P.N.,” Mr. Chien said. “They just use it to identify who the user works for.” Then the systems wait for the worker to go to a public or commercial website, and use that moment to infect their computer. Once the machine is reconnected to the corporate network, the code is deployed, in hopes of gaining access to corporate systems.
New-school security awareness training can ensure your employees have the proper training while they transition to a work from home office environment.
 Here's how it works:
Here's how it works:




