 The latest development in extortion methods by developers of Conti shows we should begin to continually expect new and innovative extortion tactics by cybercriminal gangs moving forward.
The latest development in extortion methods by developers of Conti shows we should begin to continually expect new and innovative extortion tactics by cybercriminal gangs moving forward.
The more the pressure brought to bear, the more likely the ransom will be paid. It’s the very basis for the initial data theft by Maze back in 2019, the rise of data leak sites (and the threat to publish the data), and the other methods of extortion we’ve seen that have been used to increase pressure on ransomware victims.
But new posts on Conti’s News Victims website show the ransomware gang may have added the threat of selling access to victim networks to the list of extortion tactics. The site lists posts looking for buyers that wish to access specific compromised companies.
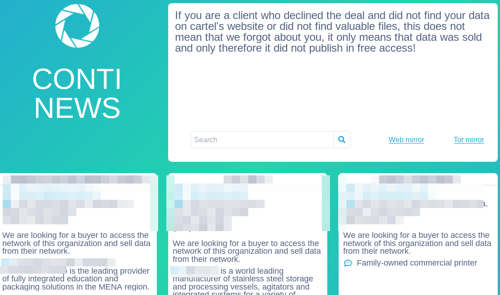
Source: Krebs on Security
While this could be a sign that the posting of data may be an extortion tactic of the past (as downloading TBs of data from a Tor takes days or weeks), it does demonstrate that ransomware gangs are continually evolving their tactics – balancing the ability to extort a ransom with an ability to easily monetize the attack in other ways should the ransom not be paid.
Either way, ransomware gangs are fully intent on making the most of the access gained to a victim network. So, it’s important that you stop these attacks before they ever start; putting Security Awareness Training into place helps ensure that those phishing emails that make if past security solutions are stopped by your last line of defense – users.
 Here's how it works:
Here's how it works:




