 IronScales just released data showing that 42% of phishing email attacks are polymorphic, enabling them to evade many security filters. The company has observed 11,733 polymorphic phishing attacks over the past twelve months.
IronScales just released data showing that 42% of phishing email attacks are polymorphic, enabling them to evade many security filters. The company has observed 11,733 polymorphic phishing attacks over the past twelve months.
Nearly 3,000 of these attacks had between 11 and 50 permutations, 704 involved between 51 and 250 permutations, and 96 of the attacks underwent between 251 and 521 alterations.
IronScales says that even small changes to an email can allow it to bypass email filters that operate by detecting malicious signatures.
“Polymorphism occurs when an attacker implements slight but significant and often random changes to an emails’ artifacts, such as its content, copy, subject line, sender name or template in conjunction with or after an initial attack has deployed,” they explain.
“This strategic approach enables attackers to quickly develop phishing attacks that trick signature-based email security tools that were not built to recognize such modifications to threats; ultimately allowing different versions of the same attack to land undetected in employee inboxes.”
The company points out that many cheap phishing kits available online now have built-in, automated polymorphic capabilities, so this behavior will likely become a standard feature in phishing campaigns. It’s a familiar pattern: the attacker adapts to the defender, and what were once advanced techniques and tools become commodities any hood can get their hands on. An aware human being, alert to the possibility of social engineering and quick to spot the scam, is the most adaptable defense.
You cultivate those skills through education. New-school security awareness training is one of the most comprehensive defenses against phishing, because it enables your employees to identify new attacks that get through your technical defenses. PRWeb has the story:
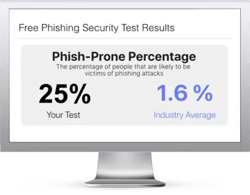
Free Phishing Security Test
Find out what percentage of your employees are Phish-prone™
Would your users fall for convincing phishing attacks? Take the first step now and find out before the bad guys do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
 Here's how it works:
Here's how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





