 Eric Howes, KnowBe4 Principal Lab Researcher, found out about another insidious bad guy trick: "If you work in IT there has undoubtedly come a dark moment when you wondered to yourself just who among your employee users would be gullible enough to click through a phishing email and potentially bring down your organization.
Eric Howes, KnowBe4 Principal Lab Researcher, found out about another insidious bad guy trick: "If you work in IT there has undoubtedly come a dark moment when you wondered to yourself just who among your employee users would be gullible enough to click through a phishing email and potentially bring down your organization.
There are ways to find out. One way is to sign up for a free Phishing Security Test, run a simulated phishing campaign against your own users, and see who clicks.
There is another way, of course. You can wait for gullible users in your organization to out themselves when they add their names to a virtual "wall of shame." And it might happen sooner than you think, because the bad guys are now running phishing campaigns that afford your users the opportunity to do just that.
Here's the setup.
Phishing and File Sharing
Malicious actors have long used file sharing sites and services to host their malicious files. When they do this, they typically use the underlying service to generate download links that anyone can click without logging in to the hosting service. Makes sense when you're blasting out thousands upon thousands phishing emails with malicious links. You want to set the table for a feast, not an intimate dinner for two.
The other thing the bad guys typically do, however, is generate their own emails instead of using the underlying hosting service to deliver their malicious links to a wide audience. Doing so reduces the chances that the service notices something is amiss (like mass spam deluges erupting from their own servers) and provides more flexibility to tailor the social engineering hook in the message body.
We've seen plenty of services abused like this: WeTransfer, Dropbox, Google Drive, etc. The hosting services eventually yank the malicious files and the links go dead.
The less imaginative and industrious among the bad guys, of course, don't even bother trying to host and distribute their malicious files via legitimate online services. They simply spoof services like Dropbox and Docusign in phishing emails, some more skillfully designed than others. Even when done well, though, such phishes are comparatively easy to spot because the embedded links don't point to Dropbox or Docusign.
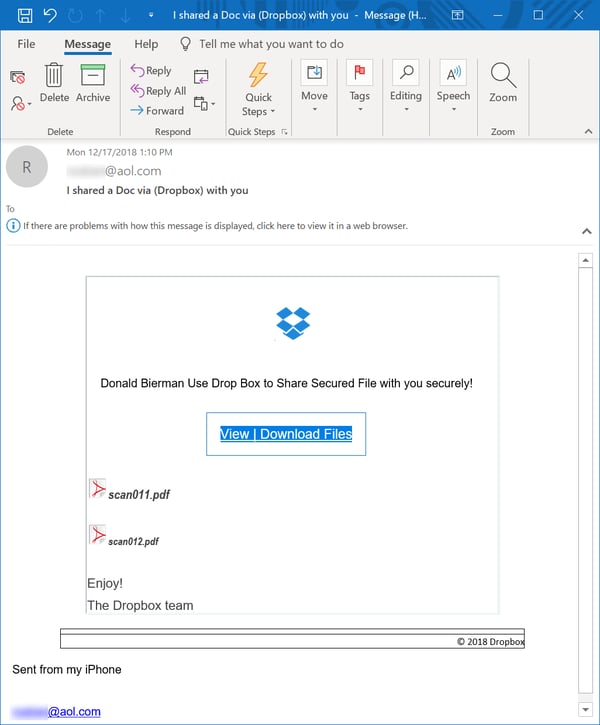
Here's a typical spoofed Dropbox phish:
The link in that malicious email leads to spoofed Dropbox download page:
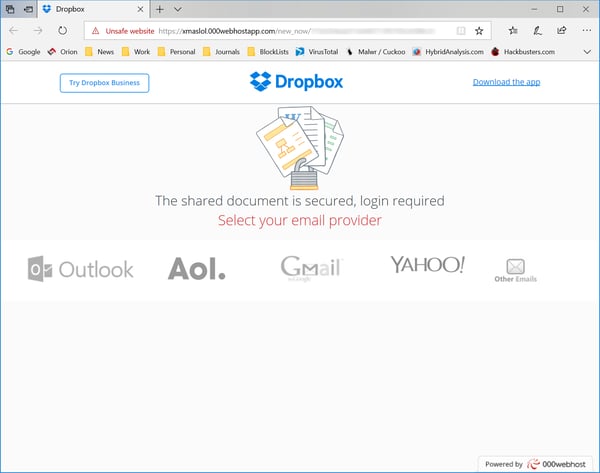
Worse, the bad guys often screw up the format of the email, occasionally even using the wrong corporate logos -- e.g., shoehorning Google, Adobe, or Microsoft logos into spoofed Dropbox emails, as in the email above. HTML gods they are not.
There are no such problems with a new round of phishing emails we recently encountered.
Phishing Users from the Inside
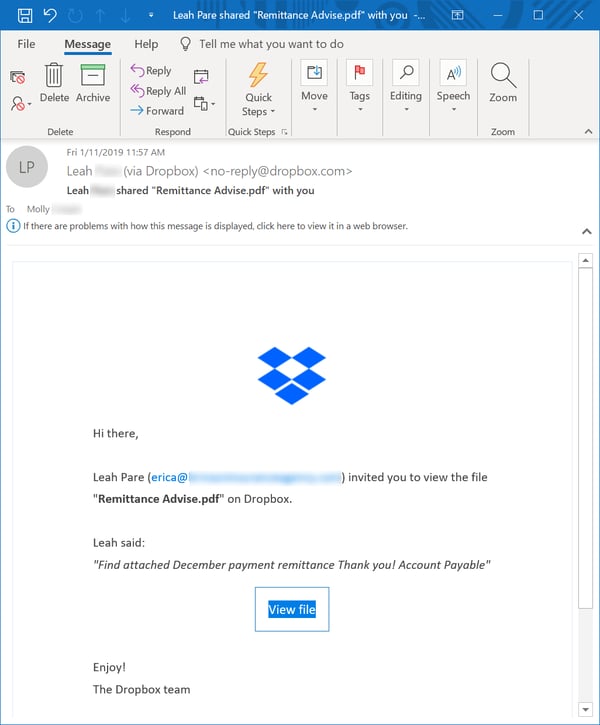
Over the past month we started noticing apparently legitimate Dropbox emails pushing links to files with names suspiciously similar to those routinely used by the bad guys. When we clicked the links to check, however, we were greeted with a demand to log in to the service. That's typically been a sign that the files involved were legit.
Still, something wasn't right here. Given the file names presented, we reckoned there was little chance those files were innocuous. So, we decided to log in to Dropbox and check if our hunch was correct. It was.
We spotted a seven Dropbox emails all pushing the same file.
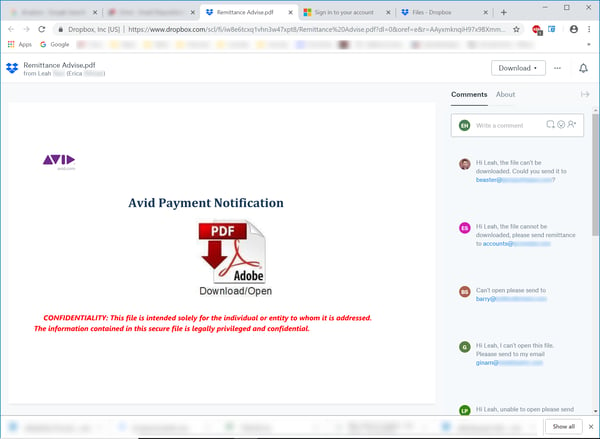
So, we logged in to Dropbox to check the file. As suspected, the file was a malicious PDF of the type usually delivered as an attachment to phishing emails.
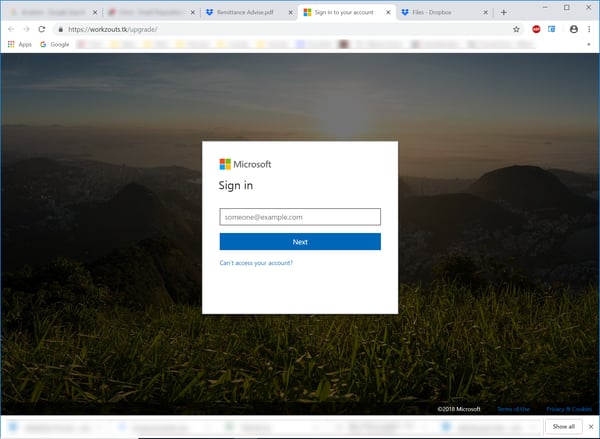
The link in that PDF opens a spoofed Microsoft login page hosted on a rather shady domain.
But there was something else we noticed.
The Wall of Shame
We were also interested to learn that we were not the first to visit to that malicious PDF on Dropbox. Look at the Comments section on the right of that PDF download page.
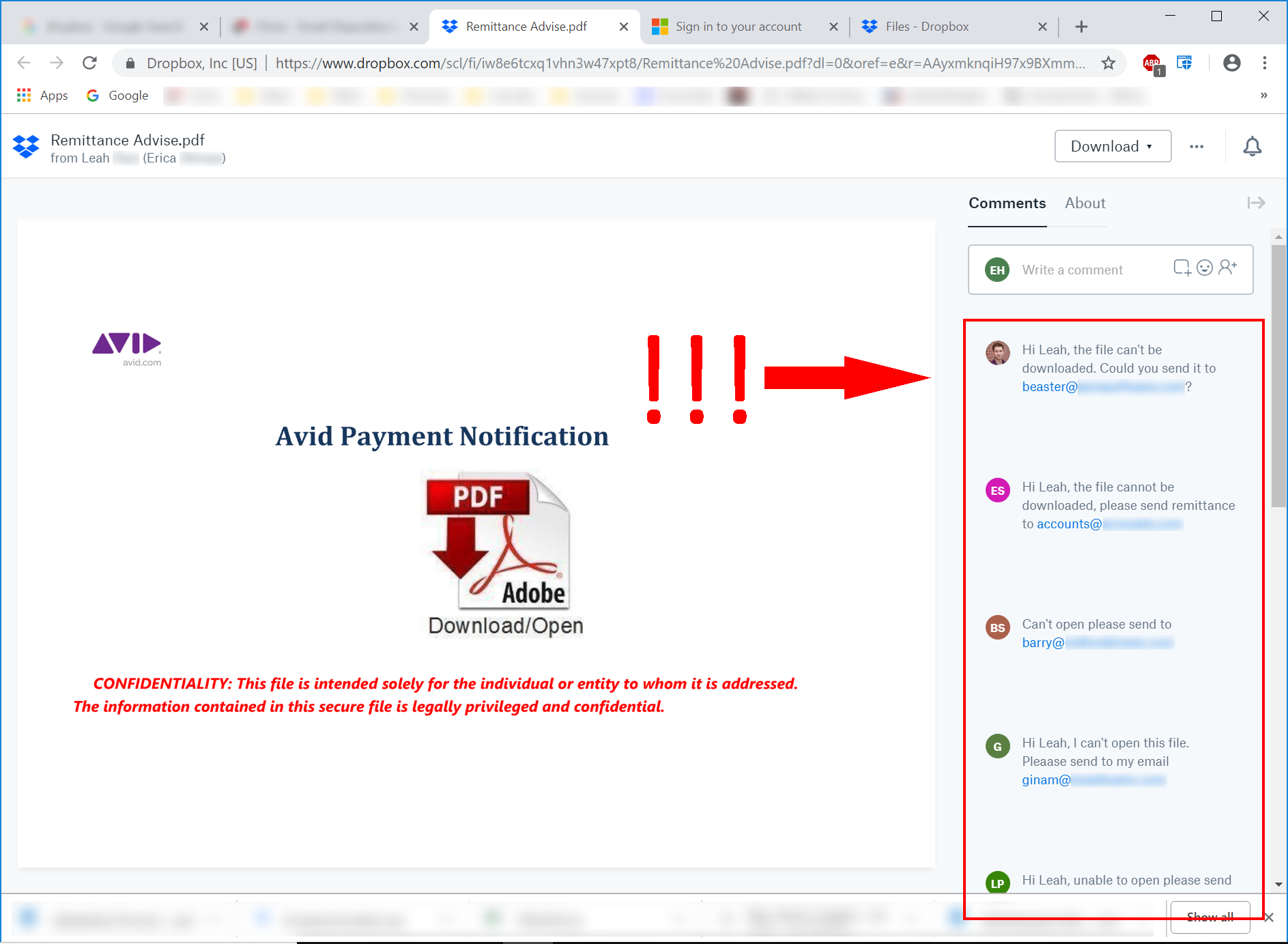
Yep, there they are. Gullible users advertising themselves as having fallen for the ruse and helpfully providing their email addresses so the bad guys can send them still more malicious files.
A Calculated Decision
So, the bad guys made a calculated decision here: abandon the publicly accessible download links; use Dropbox itself to deliver the links via official Dropbox email notices; then require users to log in to Dropbox. And do it all from a Dropbox account that is undoubtedly compromised.
In doing so, the bad guys undoubtedly narrowed the potential audience for their malicious files (not everyone will have a Dropbox account). But they gained the advantage of camouflaging their malicious links behind Dropbox itself. They got phishing emails that look credible to users (they're from Dropbox itself), and they reduced the chances that link checkers (now widely used in hosted services like Office 365 and Proofpoint, to mention but two) will be able to follow and identify the malicious links.
And, of course, they also get to enjoy good belly laugh from the spectacle of all those gullible marks outing themselves on Dropbox.
Find Out First
You shouldn't have to rely on the bad guys to bait your users into outing themselves. A free Phishing Security Test will quickly tell you who in your organization needs help dealing with cleverly crafted phishing. It will also give you a broader picture of your organization's vulnerability to phishing attacks, allowing you to roll out New-school Security Awareness Training that gets your users up to speed on how to handle the malicious emails landing in their inboxes every day.
And once your users are "woke" to the threat of phishing, you can provide the Phish Alert Button so they can alert YOU when phishing emails hit their inboxes instead of advertising to the bad guys (and the rest of the world) that they are all-too-vulnerable to phishing campaigns driven by increasingly sophisticated social engineering schemes."
I suggest you send this reminder to your users. Feel free to edit, copy/paste:
"The bad guys have come up with another way to trick you! Now they are using sites like Dropbox, Google Drive and other file hosting sites for their evil attacks. They put a malicious file on these sites, and they use that site to send you an invite to log in and open/click on that infected file. The invites look legit because they are. They really came from that site and are identical to the normal invites. So what to look out for?
- Email invites to open a shared file somewhere in the cloud that you did not ask for.
- Emails that require you to log into a site to see something important. Don't enter anything.
Remember to never click on links in emails that you did not expect or did not ask for. If you decide to log into a file sharing site like Dropbox, enter the address in your browser or use a bookmark you set yourself earlier. Think Before You Click!
Let's stay safe out there.
Warm regards,
Stu Sjouwerman
Founder and CEO,
KnowBe4, Inc





