What is a security tech stack? This is a bare-bones quick overview.
First of all, the term “stack” is used because it describes layers that deliver services and exchange information to achieve a higher level service. The concept of a “security stack” communicates that security must be an integrated set of services.
Every layer is a particular technology with its own features. The security stack needs to be designed from the ground up knowing that security is a vital network element, just like multiple blueprints (electrical, plumbing, flooring, etc.) are required to construct a safe and stable building. Whitepaper with more.
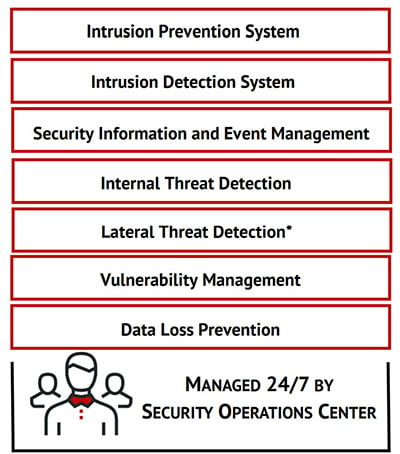
So, what would be a rock-bottom, bare minimum security stack? Here is a picture. We should add secure login to that as a fifth layer.

In general, there are a few things that CISOs agree on in the sense of bare minimum, here is a list of 5 essentials:
- Email security
- Security awareness training
- Multi-factor authentication
- A good endpoint protection tool like next-generation antivirus
- Patching and vulnerability management
But there are literally tons of other layers (tools) that in many cases should be added. Here is a picture of a security stack that a managed security service provider (MSSP) created for their customers. The layers together provide a higher level service, and include some of the bare minimum list above.
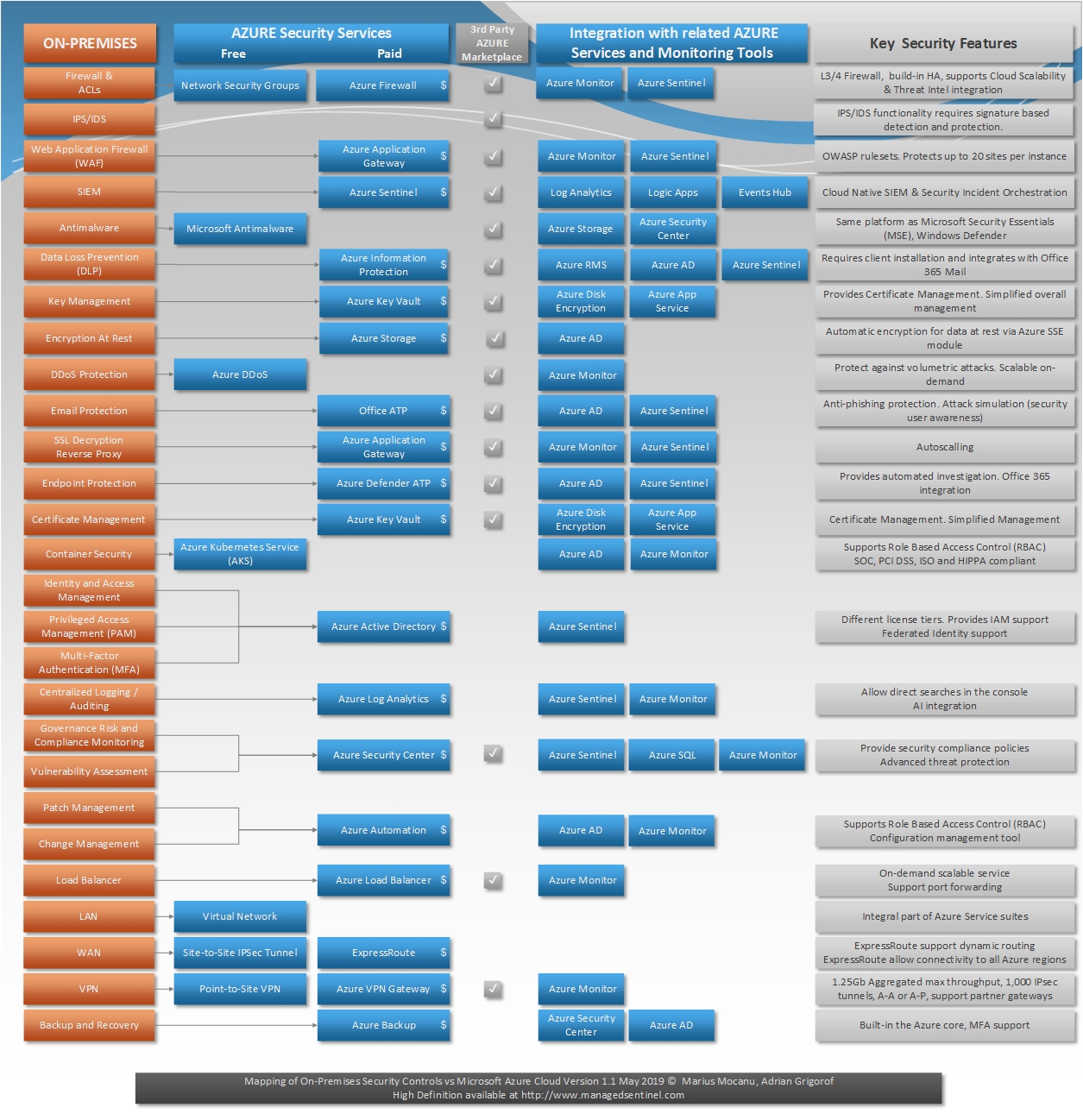
However, it can get super sophisticated! Here is an example of a list of technologies in orange on the left that gives you an idea of the potential complexity, of in this case the Azure security stack.
 Here's how it works:
Here's how it works:




