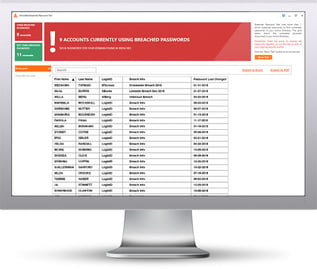
First of all, the term means that a particular password is available in a data breach on the dark web–and there are billions of breached passwords out there. KnowBe4 just released a free tool that you can run and see if any of the passwords your users are using today in Active Directory, are actually out there in a data breach.
An IT Admin asked us, so exactly what are the risks?
"One question I have though is, what is the actual risk? If a malicious actor has a users' AD password, what can they do? I know that if a user clicks a malicious link or run a malicious attachment, obviously that opens up a whole can of worms, but that's not really related to the users password being compromised. Also, at the moment our AD is not linked to the outside world so to speak, although obviously most users can access the Internet, but with restricted inbound access (no RDP or port forwarding etc.) that shouldn't be an issue.
"We will be migrating over to Office 365 and using Outlook in the cloud and I know that will then introduce a risk if passwords are known, but at the moment I'm looking for what the risk is as we stand at the moment."
Answer:
We don't know if you had any matches show up when you ran the Breached Password Test (BPT) tool, but if you did find some people actively using passwords that matched there is certainly a behavior/awareness issue to take up.
Likely that's the tip of the iceberg of what bad password practices they have because if you think about it, how did the username/password combo end up out on the dark web if your AD wasn't the source? The most logical answer to that is password re-use across sites, someone used their work email and password to sign up at some site which did get compromised.
And they probably still are... That's likely the biggest risk for any organization that has no external access allowed, it's that bad practices are likely employed on the external services your company uses, including any "gray IT" projects where users create their own cloud accounts unknown to you.
If you didn't have any active BPT matches, great! That's good news and you should just make sure people know that once a password has been used it should never be used again, everyone likes to roll back around to their favorite password because it's just human nature.
Ultimately the results of running this tool are something you should share with your users because it's *very* much a wake-up call to an employee to find out that their password is literally floating around for anyone to use.
We've seen many a dawning realization across a person's face when they think about how many times they've used similar/same password across their banking services and other sites that have private information.
If you did not get any matches with the BPT, we recommend as the next step you run the Weak Password Test companion tool to find out more about your users and their password habits, and run the Email Exposure Check Pro, to see how many email addresses of your users are floating out there in breaches.
 Here's how it works:
Here's how it works:




