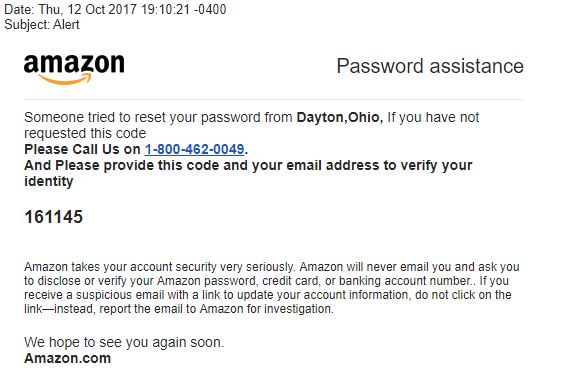
So here’s a new one: a spoofed Amazon email claiming that Amazon has detected an unauthorized attempt to reset the password on the recipient’s account. A six digit code is provided along with instructions to call a phone number to “verify your identity.” Here is a screenshot of the phishing email:
A number of users online have reported receiving this phish over the past month. Some have even called the provided phone number. They report their calls being answered by individuals speaking with a thick Indian accent who then attempts to direct them to a web site in order to input more information. Here are two scam alert sites with people filing reports:
https://www.everycaller.com/phone-number/1-800-462-0049/
https://800notes.com/Phone.aspx/1-800-462-0049
We have yet to find a user providing a detailed account of just where the scam web site is that people get redirected to, or what information is requested. Our guess at this point is that it’s either an elaborate credentials phish or the set up for a tech support scam where the bad guys inform users that they must download a RAT (remote access trojan) to allow their personnel to “clean” users' PCs of malware.
Warn your users to not fall for this new phishing scam that uses social engineering to manipulate them into allowing the bad guys into their workstation.




