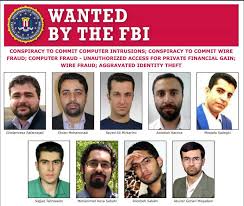
Friday morning the US Department of Justice announced that it had indicted Iran's Mabna Institute and nine of the individuals who work for it. The charges include conspiracy to commit computer intrusions, wire fraud, unauthorized access of a computer, and aggravated identity theft.
The Mabna Institute allegedly works as a contractor for Iran's Islamic Revolutionary Guard Corps. It has, Justice said in a Friday press conference, conducted a lengthy, years-long, and far-flung cyber espionage campaign against targets in some twenty-one countries, including the US. The campaign appears to have been directed toward the theft of technical information and intellectual property.
Some of the information Iran used; some of it Iran sold. The methods the Mabna Institute used in its campaign is interesting. They approached their harder targets by first compromising easier ones. The softer targets, university professors in more than three-hundred institutions around the world, were trawled with a very large phishnet.
Some hundred-thousand professors were send spear phishing attacks, and about eight thousand of them were caught. From those compromised individuals the hackers gained access to university credentials and databases. They then used what the FBI called "low and slow password spraying attacks" to move to harder targets in industry and government.
The Treasury Department also announced sanctions against the Institute and the individuals named in the indictment. The combined Justice and Treasury action represents, the Departments' representatives say, an example of the Administration's determination to impose costs on bad actors in cyberspace.
It is of course very unlikely that any of the defendants will ever see the inside of a US courtroom, still less a US prison. But the costs are real nonetheless. As the Department of Justice has pointed out, one immediate consequence of the indictment is that the defendants will effectively be unable to travel outside of Iran to any country that has an extradition agreement with the US.
The indictment holds valuable lessons for all organizations, but especially for universities. Phishing is a threat to anyone who uses email and has something of value to steal. University faculty make excellent targets. Professors also tend to kid themselves that they're immune to such threats.
They're not. They also often credit themselves with an ability to see through scams. This confidence is also often misplaced. Universities could benefit from new-school security awareness training that would create a strong human firewall.
Industry and government, who are frequent partners with universities, should consider helping academic institutions raise their security game. They are, after all, effectively a link in the supply chain. CNN has the story here: https://www.cnn.com/2018/03/23/politics/iranian-hackers-indicted-universities-government/index.html




