A large phishing campaign is distributing malicious Excel documents and utilizing irritating pop-ups to trick users into enabling macros, researchers at Lastline have found. The campaign is primarily focused on the Asia-Pacific region, and it’s using both generic spam emails and spearphishing to reach its targets. The malicious macros act as downloaders for more advanced information-stealing malware, including Agent Tesla and LokiBot.
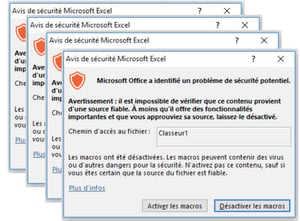
One interesting aspect of the campaign is how the documents try to compel people to run the malicious macros. When the user clicks on the document, it will be opened in Microsoft Excel. As soon as it’s opened, the document will repeatedly launch pop-up windows asking the user if they want to enable macros.
The attackers achieve this by embedding multiple Excel sheets in the document and using a Rich Text Format (RTF) control word to update each one before displaying it. This makes the document launch a new pop-up for each embedded sheet. The pop-ups will eventually cease if the user clicks “Deactivate macros” on each one, but the technique is much more persuasive than relying on a single request to allow macros.
Another notable feature of this campaign is its use of PowerShell’s Add-Type cmdlet to compile C# code and run it within the PowerShell environment. The C# code uses a common method to bypass the Windows Antimalware Scan Interface (AMSI), then downloads and executes the primary piece of malware. The Lastline researchers say the Add-Type trick allows them to avoid detection by security tools that are looking for malicious PowerShell commands.
“As discussed earlier, this technique provided the attackers with great flexibility to bypass AMSI-related detection and carry out further malicious downloads,” the researchers write. “Given its effectiveness, we expect this technique to become more popular in weaponized PowerShell payloads.”
While the attackers are increasing their malware’s ability to remain undetected by technology, the entire attack can be averted if the user knows to avoid enabling macros at all costs. New-school security awareness training can enable your employees to thwart the social engineering aspects of these attacks.
Lastline has the story: https://www.lastline.com/labsblog/infostealers-self-compiling-droppers-set-loose-unusual-spam-campaign/




