 Ok, I'll admit it, I was swept up in the moment last week and wrote a short blog post that more or less summarized the tsunami of news about that huge data breach initially reported by Cybernews. They called it the Mother of all Breaches (MOAB), and a seismic event. However, hold your horses, not so fast!
Ok, I'll admit it, I was swept up in the moment last week and wrote a short blog post that more or less summarized the tsunami of news about that huge data breach initially reported by Cybernews. They called it the Mother of all Breaches (MOAB), and a seismic event. However, hold your horses, not so fast!
This discovery sure is large, but there's way more to it than that, and it is certainly not unique. I decided to do some research and check Troy Hunt's X feed. We have worked for years with Troy, and he's the world's most prominent large data breach expert. His perspective puts this event back in its proper context. Here are a few points that he made:
- "Interesting find. Collecting and storing this data is now trivial so not a big surprise to see someone screw up their permissions and (re)leak it all.
- The term “records” is often used to describe the total number of rows in the DB and frequently doesn’t correlate to “unique email addresses”. You can have a *massive* incident with a relatively small number of unique email addresses.
- Take both record numbers and terabytes of data with a grain of salt. They make for great headlines, but they’re a superset of the volume of genuinely impactful data.
- There are *many* stashes of breaches floating around ranging from personal collections to Telegram channels to data people publish to public forums where they’re easily downloadable. That one of these stashes was perhaps inadvertently left open doesn’t really have any impact.
- This reporting is just getting stupid: “Big brands caught in ‘mother of all breaches’”. These are breaches that date back as far as more than a decade (Adobe), and they’re now in a news headline despite them already being so broadly distributed."
So, the upshot is that yes, there is a large risk of password compromise, and a large attack surface that needs to be mitigated. But nothing really new here folks, you need phishing-resistant MFA and trained users.
The original title of this blog post was: "Unprecedented Cybersecurity Alert: 26 Billion Records Exposed in Mega Data Breach" and stated: In what appears to be a digital tsunami, Cybernews has reported a colossal data breach has surfaced, unveiling a staggering 26 billion records – a figure that's hard to even fathom.
Termed as the Mother of all Breaches (MOAB), this leak is not just another incident in the cybersecurity world, it's a seismic event that dwarfs previous breaches in its sheer magnitude.
The MOAB is a compilation of information so vast that it comprises 12 terabytes of data, including user details from platforms like LinkedIn, Twitter, Weibo and Tencent.
This massive data trove is a Frankenstein's monster of sorts, stitched together from thousands of different leaks, breaches and privately sold databases. It's a huge scale, unprecedented aggregation of digital identities.
This discovery, brought to light by cybersecurity researcher Bob Dyachenko and the Cybernews team, is particularly alarming due to the open nature of the data instance. Tracing the owner seems like a daunting, if not impossible, task. But the question on everyone's mind is: is my data included in this breach?
Here’s the kicker – while much of the MOAB's content is from past breaches, it likely contains new, previously unpublished data. The scale is such that, of the 26 billion records, there's a high chance that billions of these are fresh entries, posing an even greater risk.
Researchers surmise that whoever is behind the MOAB could be a malicious actor, a data broker, or a service dealing with massive data sets. The intentions remain murky, but the implications are clear: the data could be used for a myriad of nefarious purposes, from identity theft to sophisticated phishing attacks.
This isn't just a collection of email addresses and passwords. The MOAB goes deeper, with sensitive personal information that could be a goldmine for cybercriminals. Its existence is a stark reminder of the human attack surface we face and the ever-present need for phishing-resistant MFA and and trained users.
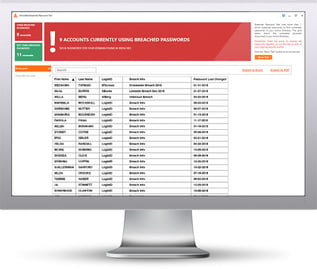 Here's how it works:
Here's how it works:




