It was all over the news, but ZDNet's Eileen Yu was one of the first. -- "Hacker is believed to have breached Uber's entire network in a social engineering attack, which one security vendor says is more extensive than the company's 2016 global data breach and access logs potentially altered."
The article continues: " A hacker on Thursday was believed to have breached multiple internal systems, with administrative access to Uber's cloud services including on Amazon Web Services (AWS) and Google Cloud (GCP).
"The attacker is claiming to have completely compromised Uber, showing screenshots where they're full admin on AWS and GCP," Sam Curry wrote in a tweet. The security engineer at Yuga Labs, who corresponded with the hacker, added: "This is a total compromise from what it looks like."
Uber since had shut down online access to its internal communications and engineering systems, while it investigated the breach, according a report by The New York Times (NYT), which broke the news. The company's internal messaging platform, Slack, also was taken offline.
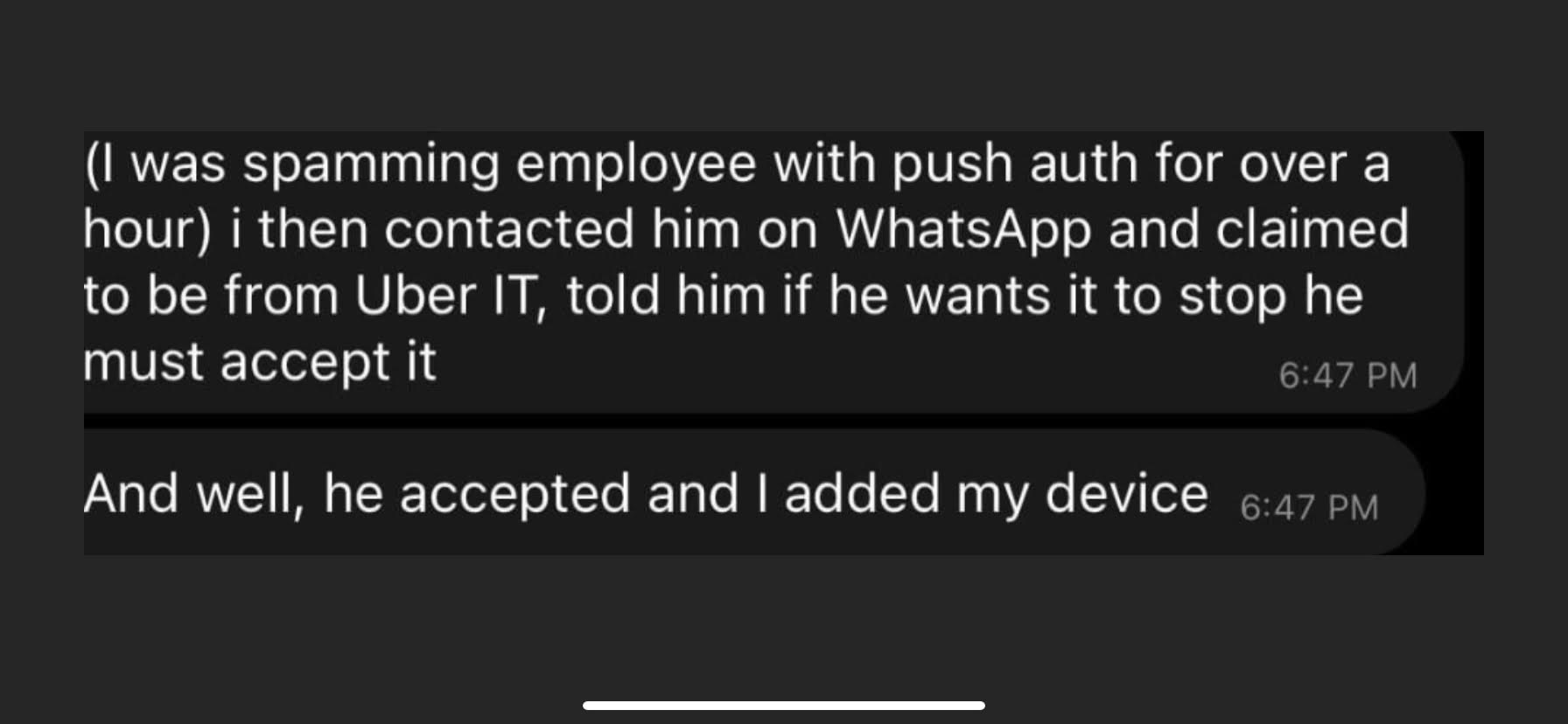
The hacker, who claimed to be 18 years old, told NYT he had sent a text message to an Uber employee and was able to persuade the staff member to reveal a password after claiming to be a corporate information technology personnel. The social engineering hack allowed him to breach Uber's systems, with the hacker describing the company's security posture as weak.
With the employee's password, the hacker was able to get into the internal VPN, said Acronis' CISO Kevin Reed in a LinkedIn post. The hacker then gained access to the corporate network, found highly privileged credentials on network file shares, and used these to access everything, including production systems, corporate EDR (endpoint detection and response) console, and Uber's Slack management interface."
Quote from WIRED: "One independent security engineer described the OneLogin account access the Uber hacker seems to have had access to as “the golden ticket jackpot.”
Don't let this happen to you. Train your users.
The full article is at ZDNet:
https://www.zdnet.com/article/uber-security-breach-looks-bad-potentially-compromising-all-systems/
Update 9/17/2022 10:31 - in-depth article by WIRED:
https://www.wired.com/story/uber-hack-mfa-phishing/
Update 9/20/2022 09:35am - Uber links breach to Lapsus$ group, blames contractor for hack
Update 9/21/2022 3:13pm - Social Engineering: How A Teen Hacker Allegedly Managed To Breach Both Uber And Rockstar Games






