 There is no doubt that ransomware is one of the top cybersecurity challenges of our lifetime. Survey after survey has revealed senior management and IT employees from the top on down, list a successful ransomware attack as their number one cybersecurity fear above all others.
There is no doubt that ransomware is one of the top cybersecurity challenges of our lifetime. Survey after survey has revealed senior management and IT employees from the top on down, list a successful ransomware attack as their number one cybersecurity fear above all others.
Ransomware attacks can be difficult to prevent and can cause costly business interruptions for months. Ransomware might be the most feared cyber threats we have faced, at least so far. But that does not mean we cannot significantly reduce the risk of a successful ransomware attack or reduce recovery costs from a successful attack.
Attend my upcoming webinar, A Master Class on IT Security: Roger Grimes Teaches Ransomware Mitigation to learn how to significantly reduce the risk of ransomware attacks.
Ransomware mitigation involves three distinct phases:
- Prevention
- Early Detection
- Recovery
I will cover each of these topics in more detail below.
Prevention
Preventing ransomware from being successfully introduced into your devices and environment is the only way to ensure that no damage is done. The most common recommended defenses from most sources say the best way to fight ransomware is with a good backup. It is not bad advice, but a backup does not stop ransomware attacks. It just helps with operational recovery. Prevention beats recovery.
A perfect backup does not even prevent ransomware extortion tactics from being successful. Today, over 96% of all ransomware attacks do what is popularly known as “double extortion.” Double extortion means ransomware usually asks for a ransom to unlock any encrypted files and/or to delete and not use any exfiltrated data. Data exfiltration can include:
- Files and databases
- Emails
- Financial statements
- Contracts
- Company, employee, and customer passwords and information
- Intellectual property
Ransomware will often use stolen customer information to initiate future attacks on the original victim’s customers and business partners and use denial-of-service (DoS) attacks and public shaming to increase the pressure on the original victim to pay the ransom. The victim will be told that if the ransom is not paid that their exfiltrated data will be used against them, given to other hackers, or simply released to the public. This is not a pretend threat. Unpaid ransoms have led to the public release of very confidential files with information that was very embarrassing to the original victim as well as their employees and customers. Clearly, ransomware is not just encrypting files any longer.
Preventing ransomware is the paramount defense. It is clear that most ransomware gains initial root access to victim devices and networks using the following methods, in increasing order of popularity:
- Social engineering, particularly phishing emails
- Unpatched software
- Compromised passwords
- Misconfigurations
- Third-party compromises
- USB keys
So, knowing that these are the primary ways that ransomware penetrates, these are the attack methods you need to mitigate first and best. Your key defenses to preventing a successful ransomware attack are:
- Aggressively mitigate social engineering
- Patch exploited software and firmware
- Use multifactor authentication (MFA) when you can
- Use non-phishable MFA where you can
- Use different, non-guessable/uncrackable passwords for every website and service where you cannot use MFA (we recommend using a password manager)
- Teach everyone how to spot rogue URLs
No other defenses will work as well. Yes, you can use antimalware software, endpoint detection and response software, firewalls, VPNs, and intrusion detection components as well, but none of them protect as well as the aforementioned bullets. In fact, it is most defenders’ inability to aggressively focus on those primary mitigations that allows ransomware attackers to be as successful as they are.
Early Detection
If you cannot prevent a ransomware attack, the next best thing is early detection. The earlier you detect an initial root compromise, the better off you are going to be in terms of cost, resources and time. Unfortunately, the most common sign of ransomware exploitation is an extortion message on someone’s screen telling them that they have ransomware and need to pay a ransom. Early detection means detecting unexplainable anomalies, including:
- Rogue executables
- Encrypted files
- Elevated group memberships
- Network connections
- Service stoppages
- Very large recent file archives
Unlike my recommendation in prevention, I think antimalware or endpoint and detection and response software can have a big impact on early detection. Endpoint and detection software is better in most scenarios than traditional antimalware software. Every device and organization should be running endpoint detection and response software that looks for and mitigates ransomware attacks.
Recovery
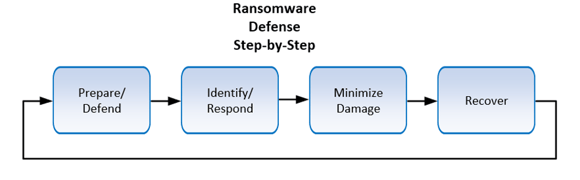
You should already have a ransomware response plan in place just in case you are exploited by ransomware. Most organizations are struck by ransomware during their lifetime, so it makes sense to have a plan just for responding to the particular needs of ransomware. The key components of a ransomware response plan are shown in the image below:
Our Ransomware Hostage Rescue Manual (https://info.knowbe4.com/ransomware-hostage-rescue-manual-0) has the details that I am about to summarize below:
- Step 1 – Start initial investigation - Is it really a ransomware attack or just a “scareware” fake screen? Is it wiperware? If it is a ransomware attack, how bad is it? What is the scope of damage? What did it do? If it is just one computer involved, perhaps an entire, complex ransomware response plan is not needed.
- Step 2 – Initiate ransomware response team - If the ransomware attack involves more than one device or location, then your ransomware response plan and team need to be activated. This will include senior management, IT management, legal, communications teams, technical IT people, other stakeholders and possibly external consultants and services.
- Step 3 – Disable networking to prevent future spread and hacker control - Better to disable networking than to turn off devices unless it is a wiperware attack.
- Step 4 – Determine full scope of the attack - Now is the time to get all the details. How bad is the attack? What did it do? What did it not do? Can you determine if data or credentials were stolen? If not, assume both were compromised.
- Step 5 – Limit damage - Do what you can to limit spread and damage.
- Step 6 – Regroup team and share any new learned details
- Step 7 – Determine response - Determine what needs to be fixed when. You usually need to start with remediating basic infrastructure (e.g., networking, DHCP, cybersecurity tools, resetting passwords, etc.). Will you be paying the ransom? How will you be recovering the encrypted data? Who needs to be notified?
- Step 8 – Recover the environment according to your business impact analysis and response plan - You may need to preserve evidence for legal issues. Do you want to take the time to add or change components in your environment to better protect it?
- Step 9 – Next steps - Try your best to figure out how the ransomware got into the environment in the first place (e.g., social engineering, unpatched software, etc.) and close any remaining vulnerabilities so it cannot happen again as easily. Review ransomware response and figure out if the ransomware response plan needs to be updated. Ransomware incident response is about gathering good information, mitigating further damage, recovery and preparing to prevent the next attempted attacks.
Summary
The first rule of ransomware response is to prevent getting exploited by ransomware in the first place. If you get exploited by ransomware, the best response is quick response by early detection. When responding, you can follow a ransomware response checklist to minimize resources, time and costs.
If you are interested in learning more about ransomware mitigation, attend my upcoming webinar, A Master Class on IT Security: Roger Grimes Teaches Ransomware Mitigation.
Register by April 12th @ 2:00 PM ET!
Don’t like to click on redirected URLs? Cut & paste this link into your browser: https://info.knowbe4.com/ransomware-mitigation-mc?partnerref=blog





