 The Intercept reported that the GRU (Russian Military Intelligence, the FSB's counterpart) executed a cyberattack on at least one U.S. voting software supplier and sent spear-phishing emails to more than 100 local election officials just days before last November’s presidential election, according to a top secret NSA report.
The Intercept reported that the GRU (Russian Military Intelligence, the FSB's counterpart) executed a cyberattack on at least one U.S. voting software supplier and sent spear-phishing emails to more than 100 local election officials just days before last November’s presidential election, according to a top secret NSA report.
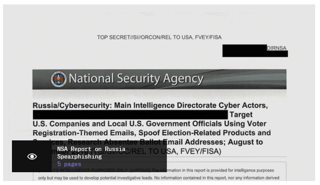
The document, (Link to PDF) which was provided anonymously to The Intercept and independently authenticated, analyzes intelligence very recently acquired by the agency about a months-long Russian intelligence cyber effort against elements of the U.S. election and voting infrastructure. The report, dated May 5, 2017, is the most detailed U.S. government account of Russian interference in the election that has yet come to light.
This NSA summary judgment is sharply at odds with Russian President Vladimir Putin’s denial last week that Russia had interfered in foreign elections.
The Spear Phishing Attack
The Intercept further explained: "As described by the classified NSA report, the Russian plan was simple: pose as an e-voting vendor and trick local government employees into opening Microsoft Word documents invisibly tainted with potent malware that could give hackers full control over the infected computers.
"But in order to dupe the local officials, the hackers needed access to an election software vendor’s internal systems to put together a convincing disguise. So on August 24, 2016, the Russian hackers sent spoofed emails purporting to be from Google to employees of an unnamed U.S. election software company, according to the NSA report.
Although the document does not directly identify the company in question, it contains references to a product made by VR Systems, a Florida-based vendor of electronic voting services and equipment whose products are used in eight states.
"The spear-phishing email contained a link directing the employees to a malicious, faux-Google website that would request their login credentials and then hand them over to the hackers. The NSA identified seven “potential victims” at the company.
While malicious emails targeting three of the potential victims were rejected by an email server, at least one of the employee accounts was likely compromised, the agency concluded. The NSA notes in its report that it is “unknown whether the aforementioned spear-phishing deployment successfully compromised all the intended victims, and what potential data from the victim could have been exfiltrated.”
There is a lot more in-depth data at The Intercept, including comments from IT security guru Bruce Schneier. Read it here, including diagrams how they did it.
It clearly shows the Russians, caught red handed.
I strongly suggest you get a quote for new-school security awareness training for your organization and find out how affordable this is. You simply have got to start training and phishing your users ASAP. If you don't, the bad guys will, because your filters never catch all of it. Get a quote now and you will be pleasantly surprised.
Don't like to click on redirected buttons? Cut & Paste this link in your browser:
https://info.knowbe4.com/kmsat_get_a_quote_now
Let's stay safe out there.
Warm regards,
Stu Sjouwerman,
Founder and CEO, KnowBe4, Inc






