We have been dealing with a vendor of ours for on-hold messages for many years. I send them a Word file with the hold messages, their studio records them, and they send us a wave file back which we upload into the voicemail console.
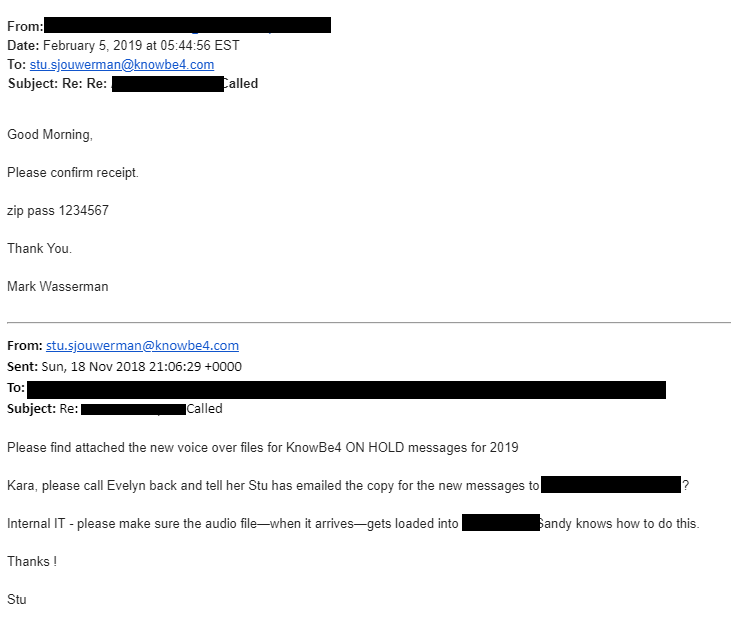
So this morning at 5 am I received an email from that vendor with an attached zip file, suggesting that was a new wave file for upload. While I have my first espresso waking up, I use an iPad Pro to handle my email and forwarded to my tech team at KnowBe4. I never looked at the Zip file. I should have known better and used the Phish Alert button instead.
Proceed With Caution
Luckily our tech team was a bit more awake at 9 am! When they came into the office, Jason walked up to me and said: "Hey, that Zip file has a Word Doc in it". That's when I realized the red flag and told him to proceed with caution. Next he said: "Hey, that Word File wants access to my contacts!" We started to see a pattern. Next Jason comments :"Hey, the default language of that Word Doc is Russian!". At that point we knew enough and sent it to our internal team for analysis.
Yup, Malicious
Our Incident Response team came back after an hour and reported that the Word doc had a macro that executed powershell, grabbed a file with a fake extension, renamed it as an exe and executed it. It is identified as "MALWARE [PTsecurity] W32.Dreambot HTTP GET Check-in"
Once executed it joined a botnet and checked-in with this ip: 194.147.34.200 (pyilgdamion.city)
Virus total now has the payload sample after we submitted it: https://www.virustotal.com/en/file/6ecb302f9dd02ffee62780bb244fc6105a4dede9ce86007e8d47e8997d7fdcd2/analysis/
Here is the simulated infection analysis: https://app.any.run/tasks/66b56fa6-c578-4267-9606-1fdb9f4bddcc
Here are the steps from download to infection, your end user only needs to do the first three and the machine is compromised
- Download zip, enter password.
- Open word doc
- enable macros
- downloads a file with .gas file extension
- renames file to a random name with .exe extension
- executes new .exe file sends http get request to pyilgdamion.city (C&C server)
Note: we have the decoded powershell command as well if anyone wants to play ;P
Conclusion
I’ve found that a good rule of thumb with password-protected ZIP files is that if the password is provided in the same email AND it’s a fairly simply one (e.g., password123 or 1234567), then it’s it’s almost surely a phish.
Stepping your users through new-school security awareness training is a must these days to make sure your network is not taken over by the bad guys.




