
SecurityWeek reported about an interesting F-Secure study showing thirty percent of CEOs from the world's largest organizations have had their company email address and password stolen from a breached service.
F-Secure researchers checked the email addresses of 200 CEOs from the world's largest organizations against a database of leaked credentials. It notes that the 30% figure increases to 63% for tech companies. Yikes.
Given the continuing tendency for users to use simple passwords and reuse the same passwords across multiple accounts, the implication is that at least some of these CEOs are at risk of losing their email accounts to cyber criminals or foreign nation state hacking groups.
The bottom line is that CEOs and their companies need to take particular care in protecting their email account passwords. F-Secure's advice is well-known good password practice:
- Use unique, long, illogical passwords that do not comprise words that could be found in hackers' word lists.
- Use a password manager to generate them (but, “Be wary of cloud-based password managers that don’t require access to the device in order to log into them”).
- Avoid social logins (if you lose the social media account, all of the associated accounts are also lost).
- Always use multi-factor authentication where it is available, avoiding SMS passcodes if possible: “Offline authenticators or hardware-based tokens are always preferred”.
Here's a link to the PDF. Good ammo for budget and it has CEO password advice from a white hat hacker.
 How weak is your CEO's password? Is it... P@ssw0rd?
How weak is your CEO's password? Is it... P@ssw0rd?
Verizon's recent Data Breach Report showed that 81% of hacking-related breaches used either stolen and/or weak passwords. Employees are the weakest link in your network security, using weak passwords and falling for phishing and social engineering attacks.
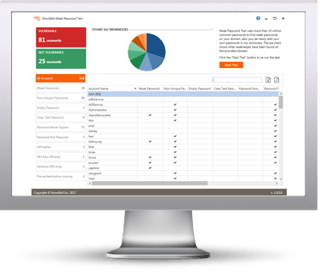
KnowBe4’s complimentary Weak Password Test (WPT) checks your Active Directory for several different types of weak password related threats.
WPT gives you a quick look at the effectiveness of your password policies and any fails so that you can take action. WPT tests against 10 types of weak password related threats for example; Weak, Duplicate, Empty, Never Expires, plus 6 more.
Here's how Weak Password Test works:
- Reports on the accounts that are affected
- Tests against 10 types of weak password related threats
- Does not show/report on the actual passwords of accounts
- Just download the install and run it
- Results in a few minutes!
This will take you 5 minutes and may give you some insights you never expected!





