Earlier this week customers using the Phish Alert Button (PAB) began reporting yet another round of spoofed KnowBe4 security awareness training emails. The emails reported are fairly straightforward spoofs, which tells us that the bad guys undoubtedly got into some user's inbox and decided that one of our training notifications would make perfect click-bait for a phishing campaign.
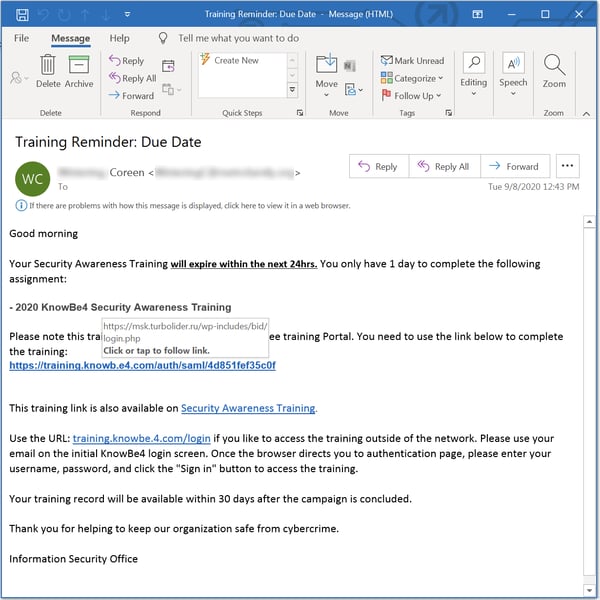
Perhaps we ought to take this as some kind of backhanded compliment. (And, for the record, we have not opened a new office in Russia.) Nonetheless, KnowBe4 customers should always be on the alert for these kinds of shenanigans.
By the time we were able to check the link, the target domain was throwing SSL configuration errors. Based solely on the structure of the URL, though, we guessing this one points to a credentials phish, which is fairly standard fare for this kind of spoof.
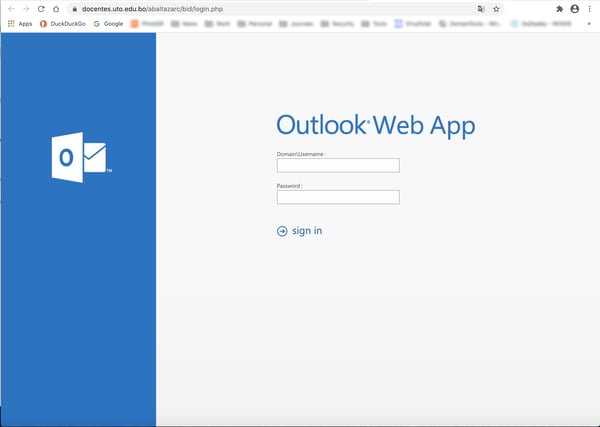
UPDATE: Based on second day's batch of emails, we can now confirm that our original assumption was in fact correct: this is a credentials phish -- for Microsoft Outlook, though, not KnowBe4. (Note that the malicious actors behind this campaign have switched to a new domain for the landing page.)
This isn't the first time malicious actors have spoofed KnowBe4. We saw a previous run of spoofed emails back in January 2019:
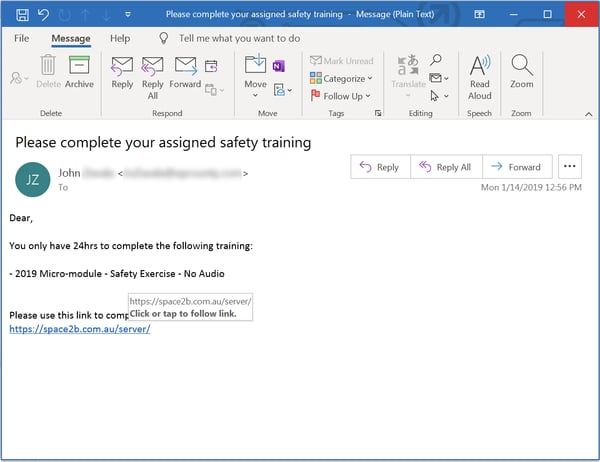
That previous round of spoofs ran for a few days and then disappeared. We're hoping this latest campaign follows the same course.
If nothing else, this particular phish should serve as a reminder that no online company or brand is immune or impervious to being spoofed as part of a malicious email campaign. Online brands, sites, and services are all vulnerable to such attacks, and your users should be completely aware of this phenomenon.
Moreover, if you've properly introduced your employees and users to KnowBe4's KMSAT training platform, they should also be thoroughly familiar with the knowbe4.com domain. Users in the habit of checking links before they click should be able to sidestep this kind of phish with ease.
If your users are still not habitually checking links, though, they need to stepped through New-school Security Awareness Training or offered remedial/followup training to get them up to speed.
 Are you aware that one of the
Are you aware that one of the
