 As part of National Tax Security Awareness Week this month, the IRS notes a surge in phishing scams aimed at stealing money or tax-related data.
As part of National Tax Security Awareness Week this month, the IRS notes a surge in phishing scams aimed at stealing money or tax-related data.
The Security Summit – which consists of the IRS, 40 state tax agencies and 20 tax industry businesses – uses the week of awareness to highlight the current state of threats to the tax industry and to provide guidance to avoid becoming a victim.
Some of the findings impacting the tax industry include:
- Nearly double the number of tax-related scam incidents were seen by the IRS in 2018 compared to 2017
- A 29% increase in tax firms that have experienced a data theft
- A 60% increase in phishing attacks
Phishing has proven to be one of the most effective methods to commit fraud, data theft, hold data for ransom, etc. The Security Summit warns specifically of scams claiming to be from the IRS or from tax firms. Emails purporting to come from the IRS demand a payment or threaten to seize the recipient’s tax refund. Those involving tax firms seek to solicit personal, tax or financial information. Additionally, the Summit warns employers of similar scams impersonating employees.
Emails impersonating the IRS can be forwarded to phishing@irs.gov.
The IRS suggests the following steps to avoid becoming a victim of phishing:
- Be Vigilant – Employers and businesses providing tax services can best protect themselves from phishing attacks by educating employees with Security Awareness Training. Employees are trained on phishing tactics in order to heightened their sense of security, making it easier to spot a malicious email and avoid becoming a victim.
- Use Security Software – the use of email, web, and DNS scanning solutions can reduce the number of potentially malicious messages that reach an Inbox.
- Use strong passwords – the emphasis is on using unique passwords for each account used.
- Use Multi-Factor Authentication – when available, use MFA to better secure access to online applications, websites, and data.
Free Phishing Security Test
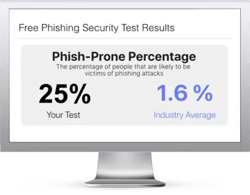
Would your users fall for convincing phishing attacks? Take the first step now and find out before the bad guys do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
 Here's how it works:
Here's how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don't like to click on redirected buttons? Cut & Paste this link in your browser:





