 A new scammer group out of Nigeria is taking additional steps to verify email addresses are valid before launching BEC campaigns designed to commit fraud.
A new scammer group out of Nigeria is taking additional steps to verify email addresses are valid before launching BEC campaigns designed to commit fraud.
How many of us have ever received an innocuous blank email, only to ignore it? According to security vendor Agari, a new group of Nigerian scammers dubbed Curious Orca have added a formal step to their attacks: once a target has been identified, they first validate the target’s email address by sending a blank email to test delivery. Taking a page right out of Marketing Automation 101, cybercriminals are treating potential targets in the same manner that companies treat their database of prospects.
Once an email has been validated, the “lead” is then supplemented with additional details, such as the CEO’s name, so that the BEC email campaign targeting that user can launch complete with tailored information to elevate its success.
Cybercriminal organizations are working more and more like traditional businesses, looking for ways to ensure their malicious content reaches their prospective target in the same way marketing organizations within companies work to ensure their marketing content reaches the right prospective customer.
BEC is serious business, estimated to have cost over $12.5B last year. Organizations need to encourage a security culture, and leverage Security Awareness Training to teach users about BEC scams, what to look for, and how to validate monetary request before falling prey to an attack.
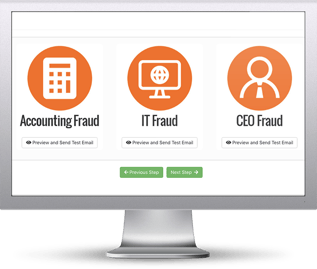 Here's how it works:
Here's how it works:




