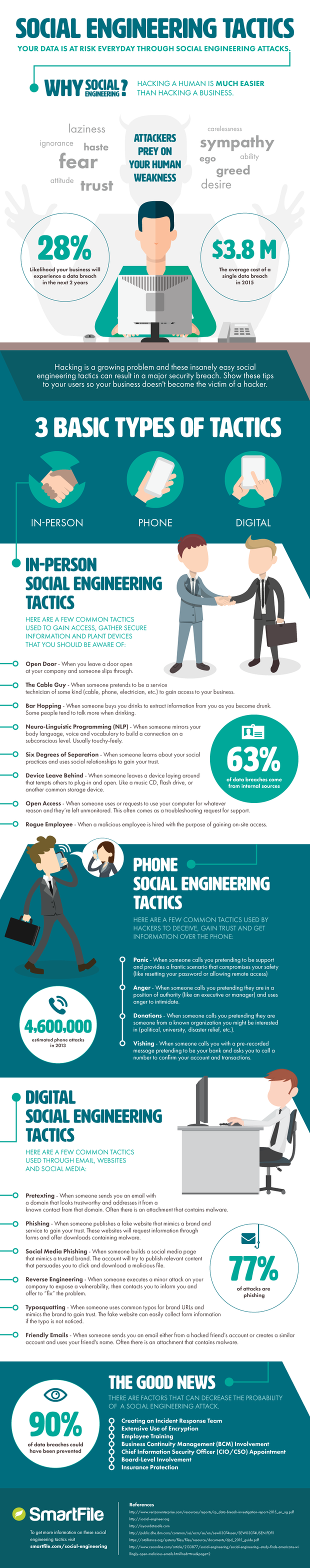
CSO Online found a great infographic created by the folks of Smartfile. They started out with: "What will the cause of your next security breach? Will it be your firewall? Will it be your VPN? Will it be your website? Nope. Chances are, your next security breach will be caused by hackers exploiting someone within your organization.
The fact is, it’s "easier to trick someone into opening an email and exploiting a vulnerability that way, or convincing an unsuspecting assistant to provide a few useful bits of information, than it is to directly attack a web application or network connection," writes George V. Hulme in his Social Engineering Survival Guide."
This new infographic from cloud file sharing provider SmartFile, clearly explains 18 common social engineering tactics. This is great security awareness training so you can spot them in the wild:
Related Pages: Social Engineering




