 The attack dubbed “PhishPoint” by Cloud Security vendor Avanan demonstrates the craftiness and extent cybercriminals will go to in order to harvest Office 365 credentials.
The attack dubbed “PhishPoint” by Cloud Security vendor Avanan demonstrates the craftiness and extent cybercriminals will go to in order to harvest Office 365 credentials.
I’ve talked about how context can be a major influencer in the success of any attack. This latest phishing attack uses several familiar aspects of Office 365 to lull potential victims into an assumption everything is above board.
Here’s how the PhishPoint attack works, according to Avanan:
- The user receives the malicious email – They confirm there is often the use of URGENT or ACTION REQUIRED to instill a sense of immediacy to respond. The email contains a link to a SharePoint Online-based document
- The link directs to SharePoint – Attackers are using true-to-form SharePoint Online-based URLS, which adds credibility and legitimacy to the email and link, since the user is being directed to a known-good hosting site.
- Users are shown a OneDrive prompt – The SharePoint file impersonates a request to access a OneDrive file (again, a known cloud entity), with an "Access Document" hyperlink that is actually a malicious URL, as shown below.
-
Users are presented with an Office 365 logon screen – Here is where the scam takes place. Using a very authentic-looking logon page where the cybercriminals harvest the user’s credentials.
What makes this attack so evil is that even Microsoft didn’t see this one coming. While they scan emails for suspicious links and attachments, a link to their own SharePoint Online wouldn’t be considered malicious. And, since Microsoft isn’t scanning files hosted on SharePoint, they left attackers with an easy means to utilize the very platform on which they are trying to con users of their credentials.
Users stepped through new-school Security Awareness Training have a better chance of spotting the telltale signs of malice. In this specific scam, several factors stood out:
- The email was unsolicited and had a generic subject of “<person> has sent you a OneDrive for Business file”
- Opening the document required several user-initiated steps
- The URL for the logon page wasn’t on the office365.com domain
This scam represents the risk associated with cloud-based applications. Using context and services users are familiar with, scammers can take advantage of the lowered level of alertness and gain access to corporate resources online – all without the organization ever knowing.
I suggest you send the following to any of your employees that use O365. You're welcome to copy, paste, and/or edit:
Be on alert! The bad guys have a new way of stealing your login credentials. They target you by sending you an invite via email to open a SharePoint document. The link takes you to an actual SharePoint page where you will see a OneDrive prompt. The prompt will have an “Access Document” link in it- don’t click this link!
This link is malicious and will take you to a fake Office 365 login screen. Any credentials you enter here will be sent to the bad guys. Don't be tricked!
Whenever you're submitting login credentials to any site, make sure to check the URL of the page for accuracy. Also, remember to always hover over links to see where they are taking you. Remember, Think Before You Click.
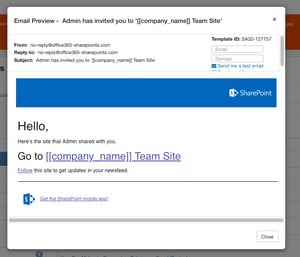
For KnowBe4 customers that use O365, we have created a template you can use to inoculate your users, and suggest you send this immediately on Monday. The template is called SharePoint: Admin has invited you to '[[company_name]] Team Site' and it lives in the Current Events category.
Here are a few more Current Events we suggest to send to your users:
- Sadly, we lost Aretha Franklin today. Scammers take advantage of tragic celebrity news to trick you into clicking.
- Newsweek: LEGENDARY SINGER DIES AT 76, SONG LEFT UNHEARD (Link)
- Kids are back in school and "back to school" specials are in full swing. Here's an offer that is too good to refuse.
- Best Buy: Back to School Specials PLUS $150 OFF ALL Laptops! (Link)
- A recruiting incentive from the newly-formed Space Force lists all the exciting details of how to join the new "out of this world" defense force.
- U.S. Department of Space Force: OFFICIAL MAIL: U.S. Department of Space Force Recruiting Incentive (Link)
- With certain businesses and even some cities banning plastic straw use, this is a timely, fake news headline to catch your users' attention.
- CNN NEWS: First Straw Ban Arrest (Link)
Stu Takes A CakeDive."
Stu




