KnowBe4 customers run millions of phishing tests per year, and we report at least quarterly on the latest top-clicked phishing email subjects so our customers know what the highest-risk phishing templates are. That way they can keep up with current threats and innoculate their last line of defense, their users, against the most prevalent social engineering attacks.
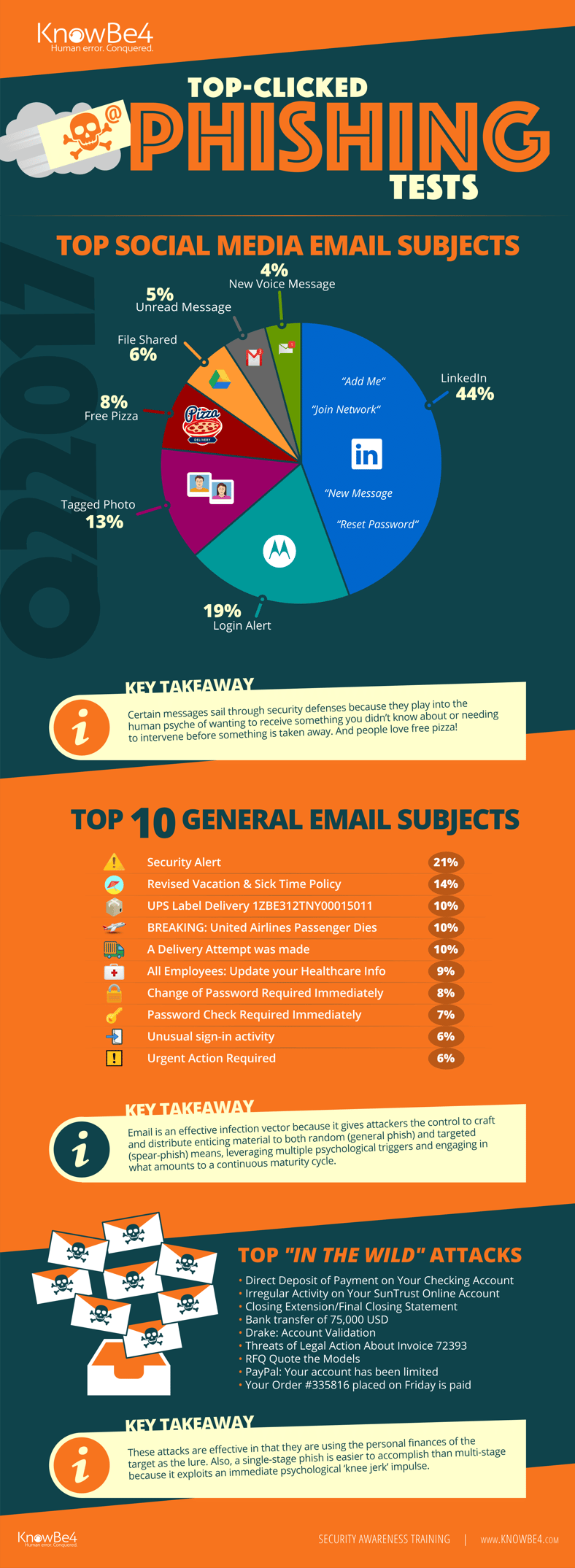
This infographic shows the most frequently clicked phishing emails from Q2 2017 in 3 separate categories: subjects related to social media, general emails and 'In The Wild' attacks that we received from our customers by employees clicking the Phish Alert Button on real phishing emails and sending the email to us for analysis.
While the results show that users click most frequently on business-related subject lines (“Security Alert” is the highest ranked at 21 percent), they still click with alarming frequency on subject lines completely unrelated to work topics:
Note that the last category of emails have made it through all the filters and into the inbox of the employee. A multi-layered defense is critical because each layer has different points of effectiveness and ineffectiveness. That is one of the reasons we continue to remind IT pros that creating a human firewall is an essential last line of defense which you cannot do without.
How Can This Help My Organization?
Armed with this data, KnowBe4 customers can set up phishing campaigns using templates related to these subjects to strengthen their human firewall. We recommend starting with 1- and 2-star level tests --these are easier to spot -- and over a 12-month period increase the difficulty level to 4- and 5-star templates which are much harder to identify.
You can even target specific groups, departments, and/or individuals with phish of differing maturity levels. That can allow security leaders to inject training at a maturity level that is most likely to help each group – and it also allows for some gamification.
Phishing Emails Remain the #1 Infection Vector
According to Osterman Research, email has been the number one infection vector since 2014. It’s an effective method because it gives attackers more control than simply placing traps on the web and hoping that people will fall for them. Instead, attackers craft and distribute enticing material using both random and targeted means. This method gives the cybercriminals greater control in selecting potential victims, leveraging multiple psychological triggers and engaging in what amounts to a continuous maturity cycle.
 Here's how it works:
Here's how it works:




