Criminals are still using hijacked GoDaddy domains to launch large-scale spam campaigns, despite GoDaddy taking steps last month to address the authentication flaw exploited by the attackers, according to Brian Krebs.
Krebs first reported on the authentication weakness on January 22nd, when he outlined two massive spam campaigns during 2018 that were very successful at getting into people’s inboxes. Their success was due to the fact that the emails were sent through trusted but dormant domains, many of which were registered and owned by Fortune 500 companies.
Anti-spam researcher Ron Guilmette discovered that nearly all of these domains had used GoDaddy’s DNS service at some point. The spammers had realized that they could add domains to their GoDaddy accounts without proving that they owned the domains. GoDaddy quickly addressed the issue and said the flaw had been fixed, although it didn’t provide details for security reasons.
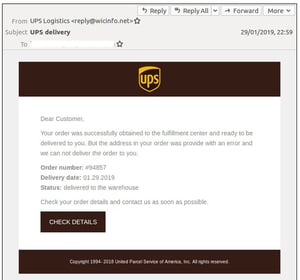
At the beginning of February, however, another large-scale spam campaign was observed using hijacked GoDaddy domains to distribute phishing emails laden with the GandCrab ransomware. A GoDaddy spokesperson told Krebs that this campaign was using previously-hijacked domains that the company had missed. He added that GoDaddy believes it has fixed the original domain-hijacking flaw, but they’re investigating to see if there are other ways through which attackers can accomplish the same result.
While GoDaddy works to shut down this activity, however, the same authentication flaw very likely affects most other major DNS providers. Organizations should be aware that some malicious emails will get through their spam filters. New-school security awareness training can help your employees recognize phishing emails that end up in their inboxes.
KrebsOnSecurity has the story: https://krebsonsecurity.com/2019/02/crooks-continue-to-exploit-godaddy-hole/
Discover dangerous look-alike domains that could be used against you!
 Since look-alike domains are a dangerous vector for phishing attacks, it's top priority that you monitor for potentially harmful domains that can spoof your domain.
Since look-alike domains are a dangerous vector for phishing attacks, it's top priority that you monitor for potentially harmful domains that can spoof your domain.
Here's how it's done:
1. Identify Look-Alike Domains
View the detailed results of look-alike domains found similar to your primary email domain. From this stage, you can easily identify the sites that are running mail or web servers and even view the WHOIS information if you decide you need to track down the owner of a domain.
2. Quiz Your Users
With your look-alike results you can now generate a real-world online assessment test to send to your users. Get the results to see what your users are able to recognize as “safe” domains for your organization and understand how security-aware your users are when it comes to identifying potentially fraudulent or phishy domains.
Get your results in just a few minutes.
Don't like to click on redirected buttons? Copy & paste this link into your browser:





